An intrusion detection system (IDS) is a device or software application that monitors a network or systems for malicious activity or policy violations. Any malicious activity or violation is typically reported either to an administrator or collected centrally using a security information and event management (SIEM) system. A SIEM system combines outputs from multiple sources, and uses alarm filtering techniques to distinguish malicious activity from false alarms.
Network security consists of the policies and practices adopted to prevent and monitor unauthorized access, misuse, modification, or denial of a computer network and network-accessible resources. Network security involves the authorization of access to data in a network, which is controlled by the network administrator. Users choose or are assigned an ID and password or other authenticating information that allows them access to information and programs within their authority. Network security covers a variety of computer networks, both public and private, that are used in everyday jobs; conducting transactions and communications among businesses, government agencies and individuals. Networks can be private, such as within a company, and others which might be open to public access. Network security is involved in organizations, enterprises, and other types of institutions. It does as its title explains: It secures the network, as well as protecting and overseeing operations being done. The most common and simple way of protecting a network resource is by assigning it a unique name and a corresponding password.

Snort is a free open source network intrusion detection system (IDS) and intrusion prevention system (IPS) created in 1998 by Martin Roesch, former founder and CTO of Sourcefire. Snort is now developed by Cisco, which purchased Sourcefire in 2013, at which Roesch is a chief security architect.
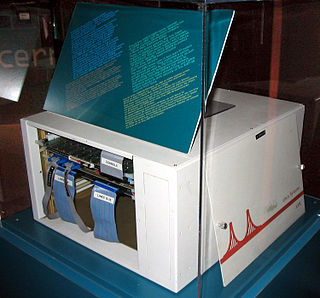
Cisco PIX was a popular IP firewall and network address translation (NAT) appliance. It was one of the first products in this market segment.
In computing, syslog is a standard for message logging. It allows separation of the software that generates messages, the system that stores them, and the software that reports and analyzes them. Each message is labeled with a facility code, indicating the software type generating the message, and assigned a severity level.
In computer log management and intelligence, log analysis is an art and science seeking to make sense out of computer-generated records. The process of creating such records is called data logging.
OSSEC is a free, open-source host-based intrusion detection system (HIDS). It performs log analysis, integrity checking, Windows registry monitoring, rootkit detection, time-based alerting, and active response. It provides intrusion detection for most operating systems, including Linux, OpenBSD, FreeBSD, OS X, Solaris and Windows. OSSEC has a centralized, cross-platform architecture allowing multiple systems to be easily monitored and managed. OSSEC has a log analysis engine that is able to correlate and analyze logs from multiple devices and formats.
A virtual security switch is a software Ethernet switch with embedded security controls within it that runs within virtual environments such as VMware vSphere, Citrix XenDesktop, Microsoft Hyper-V and Virtual Iron. The primary purpose of a virtual security switch is to provide security measures such as isolation, control and content inspection between virtual machines.

Information Technology Specialist or Information Systems Operator-Analyst is a Military Occupational Specialty (MOS) in the United States Army. Information Technology Specialists have the responsibility of maintaining, processing and troubleshooting military computer systems and operations.

An information security operations center is a facility where enterprise information systems are monitored, assessed, and defended.
Aanval is a commercial SIEM product designed specifically for use with Snort, Suricata, and Syslog data. Aanval has been in active development since 2003 and remains one of the longest running Snort capable SIEM products in the industry.
CimTrak is computer software for file integrity monitoring and regulatory compliance auditing. It assists in ensuring the availability and integrity of critical IT assets by detecting the root-cause and responding immediately to any unexpected changes to the host operating system, applications, and network devices located on the IT infrastructure. CimTrak works cross-platform and is supported on multiple Windows, Linux, Unix, and Macintosh operating systems. It is licensed as commercial software.
In computer networking, Cisco ASA 5500 Series Adaptive Security Appliances, or simply Cisco ASA, is Cisco's line of network security devices introduced in May 2005, that succeeded three existing lines of popular Cisco products:
Sagan is an open source (GNU/GPLv2) multi-threaded, high performance, real-time log analysis & correlation engine developed by Quadrant Information Security that runs on Unix operating systems. It is written in C and uses a multi-threaded architecture to deliver high performance log & event analysis. Sagan's structure and rules work similarly to the Sourcefire Snort IDS/IPS engine. This allows Sagan to be compatible with Snort rule management software and give Sagan the ability to correlate with Snort IDS/IPS data. Sagan can record events to the Snort "unified2" output format which makes Sagan compatible with user interfaces such as Snorby, Sguil, BASE and proprietary consoles
Rainer Gerhards is a German software engineer, network engineer, and protocol designer best known for his Computer data logging work including Rsyslog and Reliable Event Logging Protocol. He began developing Rsyslog in 2004, to forward log messages in an Internet Protocol Network from UNIX and Unix-like computer systems. In 1988, Gerhards founded the company RG Informationssysteme, which was later rebranded as Adiscon GmbH in 1997.
The following outline is provided as an overview of and topical guide to computer security:

Endian Firewall is an open-source router, firewall and gateway security Linux distribution developed by the South Tyrolean company Endian. The product is available as either free software, commercial software with guaranteed support services, or as a hardware appliance.

Octopussy, also known as 8Pussy, is a free and open-source computer-software which monitors systems, by constantly analyzing the syslog data they generate and transmit to such a central Octopussy server. Therefore, software like Octopussy plays an important role in maintaining an ISMS within ISO/IEC 27001-compliant environments.

IPFire is a hardened open source Linux distribution that primarily performs as a router and a firewall; a standalone firewall system with a web-based management console for configuration.