Related Research Articles
Adware, often called advertising-supported software by its developers, is software that generates revenue for its developer by automatically generating online advertisements in the user interface of the software or on a screen presented to the user during the installation process. The software may generate two types of revenue: one is for the display of the advertisement and another on a "pay-per-click" basis, if the user clicks on the advertisement. Some advertisements also act as spyware, collecting and reporting data about the user, to be sold or used for targeted advertising or user profiling. The software may implement advertisements in a variety of ways, including a static box display, a banner display, a full screen, a video, a pop-up ad or in some other form. All forms of advertising carry health, ethical, privacy and security risks for users.
SourceForge is a web service that offers software consumers a centralized online location to control and manage open-source software projects and research business software. It provides source code repository hosting, bug tracking, mirroring of downloads for load balancing, a wiki for documentation, developer and user mailing lists, user-support forums, user-written reviews and ratings, a news bulletin, micro-blog for publishing project updates, and other features.

VideoLAN is a non-profit organization which develops software for playing video and other media formats. It originally developed two programs for media streaming, VideoLAN Client (VLC) and VideoLAN Server (VLS), but most of the features of VLS have been incorporated into VLC, with the result renamed VLC media player.

FileZilla is a free and open-source, cross-platform FTP application, consisting of FileZilla Client and FileZilla Server. Clients are available for Windows, Linux, and macOS. Both server and client support FTP and FTPS, while the client can in addition connect to SFTP servers. FileZilla's source code is hosted on SourceForge.
CNET Download is an Internet download directory website launched in 1996 as a part of CNET. Initially it resided on the domain download.com, and then download.com.com for a while, and is now download.cnet.com. The domain download.com attracted at least 113 million visitors annually by 2008 according to a Compete.com study.
Browser hijacking is a form of unwanted software that modifies a web browser's settings without a user's permission, to inject unwanted advertising into the user's browser. A browser hijacker may replace the existing home page, error page, or search engine with its own. These are generally used to force hits to a particular website, increasing its advertising revenue.

Zango,, formerly ePIPO, 180solutions and Hotbar, was a software company that provided users access to its partners' videos, games, tools and utilities in exchange for viewing targeted advertising placed on their computers. Zango software is listed as adware by Symantec, and is also labeled as a potentially unwanted program by McAfee. Zango was co-founded by two brothers: Keith Smith, who served as the CEO; and Ken Smith, who served as the CTO.

Adaware, formerly known as Lavasoft, is a software development company that produces spyware and malware detection software, including Adaware. It operates as a subsidiary of Avanquest, a division of Claranova.
A browser extension is a software module for customizing a web browser. Browsers typically allow users to install a variety of extensions, including user interface modifications, cookie management, ad blocking, and the custom scripting and styling of web pages.
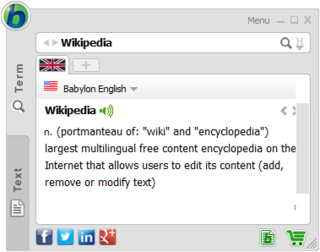
Babylon is a computer dictionary and translation program developed by the Israeli company Babylon Software Ltd. based in the city of Or Yehuda. The company was established in 1997 by the Israeli entrepreneur Amnon Ovadia. Its IPO took place ten years later. It is considered a part of Israel's Download Valley, a cluster of software companies monetizing "free" software downloads through adware. Babylon includes in-house proprietary dictionaries, as well as community-created dictionaries and glossaries. It is a tool used for translation and conversion of currencies, measurements and time, and for obtaining other contextual information. The program also uses a text-to-speech agent, so users hear the proper pronunciation of words and text. Babylon has developed 36 English-based proprietary dictionaries in 21 languages. In 2008–2009, Babylon reported earnings of 50 million NIS through its collaboration with Google.

CCleaner, developed by Piriform Software, is a utility used to clean potentially unwanted files and invalid Windows Registry entries from a computer. It is one of the longest-established system cleaners, first launched in 2004. It was originally developed for Microsoft Windows only, but in 2012, a macOS version was released. An Android version was released in 2014.
Privacy-invasive software is software that violates the user's privacy, ranging from legitimate software to malware. Privacy-invasive software is a category of software that ignores its users' right to be left alone and that is distributed with a specific intent, often of a commercial nature, which negatively affects its users.However, the software does not only "ignore" security checks, protocols and procedures, but they are engineered to forcibly or stealthily attack mechanical, manual or automated systems and gain operational control of the systems put in place so that they easily gain access to any and all information in and about a system and reads it back to the attacker.
Pre-installed software is software already installed and licensed on a computer or smartphone bought from an original equipment manufacturer (OEM). The operating system is usually factory-installed, but because it is a general requirement, this term is used for additional software apart from the bare necessary amount, usually from other sources.

Chrome Web Store is Google's online store for its Chrome web browser. As of 2022, Chrome Web Store hosts about 123,000 extensions and 29,000 themes.

Genieo Innovation is an Israeli company, specializing in unwanted software which includes advertising and user tracking software, commonly referred to as a potentially unwanted program, adware, privacy-invasive software, grayware, or malware. They are best known for Genieo, an application of this type. They also own and operate InstallMac which distributes additional 'optional' search modifying software with other applications. In 2014, Genieo Innovation was acquired for $34 million by Somoto, another company which "bundles legitimate applications with offers for additional third party applications that may be unwanted by the user". This sector of the Israeli software industry is frequently referred to as Download Valley.
InstallCore was an installation and content distribution platform created by ironSource, including a software development kit (SDK) for Windows and Mac OS X. The program allowed those using it for distribution to include monetization by advertisements or charging for installation, and made its installations invisible to the user and its anti-virus software.
Superfish was an advertising company that developed various advertising-supported software products based on a visual search engine. The company was based in Palo Alto, California. It was founded in Israel in 2006 and has been regarded as part of the country's "Download Valley" cluster of adware companies. Superfish's software is malware and adware. The software was bundled with various applications as early as 2010, and Lenovo began to bundle the software with some of its computers in September 2014. On February 20, 2015, the United States Department of Homeland Security advised uninstalling it and its associated root certificate, because they make computers vulnerable to serious cyberattacks, including interception of passwords and sensitive data being transmitted through browsers.
Download Valley is a cluster of software companies in Israel, producing and delivering adware to be installed alongside downloads of other software. The primary purpose is to monetize shareware and downloads. These software items are commonly browser toolbars, adware, browser hijackers, spyware, and malware. Another group of products are download managers, possibly designed to induce or trick the user to install adware, when downloading a piece of desired software or mobile app from a certain source.
The SourceForge Installer is a discontinued piece of software that was included in some downloads from SourceForge. It was often bundled with adware and crapware designed to trick people into installing unwanted software. SourceForge has been criticized about its use of this installer. Opinions of this feature vary, with some complaining about users not being as aware of what they are getting or being able to trust the downloaded content, whereas others see it as a reasonably harmless option that keeps individual projects and users in control.
Fireball is a browser hijacking malware discovered by the security company Check Point. It takes over target browsers and turns them into zombies.
References
- 1 2 "PUP Criteria". Malwarebytes. Retrieved 13 February 2015.
- ↑ "Rating the best anti-malware solutions". Arstechnica. 15 December 2009. Retrieved 28 January 2014.
- ↑ "Threat Encyclopedia – Generic Grayware". Trend Micro. Retrieved 27 November 2012.
- 1 2 "Mind the PUP: Top download portals to avoid". EMSISOFT. March 11, 2015. Retrieved May 4, 2015.
- 1 2 "U.S. government urges Lenovo customers to remove Superfish software". Reuters. February 20, 2015. Archived from the original on February 20, 2015. Retrieved February 20, 2015.
- ↑ CDT Files Complaints Against Major Adware Distributor (archived) January 27, 2006
- ↑ 3. IronSource, Downloads Ltd Calcalist, Assaf Gilad. April 15, 2013
- ↑ Appelberg, Shelly (8 August 2014). "Israel's Download Valley Companies See Hard Times Ahead". Haaretz.
- ↑ Hirschauge, Orr (15 May 2014). "Conduit Diversifies Away From 'Download Valley'". Wall Street Journal.
- ↑ "Meet Israel's low-profile unicorn: ironSource". 18 January 2015.
- ↑ "62% of the Top 50 Download.com applications bundle toolbars and other PUPs". EMSISOFT blog. 26 Feb 2015.
- ↑ "Google Investigation: Ad Injection Is Infesting Millions of Devices". adage.com. 4 August 2016.
- ↑ "Google Research". 2015.
- ↑ "Malwarebytes Potentially Unwanted Program Criteria". Malwarebytes.
- ↑ "Ad Injection at Scale: Assessing Deceptive Advertisement Modifications" (PDF). Archived from the original (PDF) on 2015-06-05. Retrieved 2015-06-03.
- ↑ "Superfish injects ads into 5 percent of all Google page views". PCWorld. 2015-05-07. Retrieved 2016-07-04.
- ↑ "Superfish injects ads in one in 25 Google page views". CIO. 2015-05-07. Retrieved 2016-07-04.
- ↑ "Adware vendors buy Chrome Extensions to send ad- and malware-filled updates". Ars Technica. 17 January 2014. Retrieved 20 January 2014.
- ↑ Winkler, Rolfe (19 January 2014). "Google Removes Two Chrome Extensions Amid Ad Uproar". Wall Street Journal. Retrieved 20 January 2014.
- ↑ Bruce Schneier (21 Jan 2014). "Adware Vendors Buy and Abuse Chrome Extensions".
- ↑ "Alert: Lenovo "Superfish" Adware Vulnerable to HTTPS Spoofing". United States Computer Emergency Readiness Team. February 20, 2015. Retrieved February 20, 2015.
- ↑ "Gefährliche Adware: Mehr als ein Dutzend Anwendungen verbreiten Superfish-Zertifikat" [Dangerous Aware: More than a Dozen Applications spreading Superfish Certificate]. Heise Security . February 24, 2015. Retrieved May 5, 2015.
- ↑ "Android trojan sends premium SMS messages, targets U.S. users for first time". SC Magazine.
- ↑ "New malware attack through Google Play". MediaCenter Panda Security. 13 February 2014.
- ↑ Swati Khandelwal (15 February 2014). "300000 Android Devices infected by Premium SMS-Sending Malware". The Hacker News - Biggest Information Security Channel.
- ↑ Van der Sar, Ernesto (March 18, 2021). "uTorrent Continues to be Flagged as 'Severe Threat' and It's Not alone". TorrentFreak. Archived from the original on 2021-07-28. Retrieved 1 August 2021.
- ↑ Microsoft Security Intelligence Report Volume 13, p14
- 1 2 "Yes, Every Freeware Download Site is Serving Crapware (Here's the Proof)". HowToGeek.com. 21 Jan 2015.
Sadly, even on Google all the top results for most open source and freeware are just ads for really terrible sites that are bundling crapware, adware, and malware on top of the installer. Most geeks will know that they shouldn't click on the ads, but obviously enough people are clicking those ads for them to be able to afford to pay the high per-click prices for Google AdWords.
- ↑ Brian Krebs (2011-12-06). "Download.com Bundling Toolbars, Trojans?". Krebs on security. Retrieved 2015-05-04.
- 1 2 Gordon Lyon (2012-06-27). "Download.com Caught Adding Malware to Nmap & Other Software" . Retrieved 2015-05-04.
we suggest avoiding CNET Download.com entirely
- ↑ Darren Pauli (2014-07-08). "Insecure AVG search tool shoved down users' throats, says US CERT". The Register. Retrieved 2015-05-04.
Sneaky 'foistware' downloads install things you never asked for
- ↑ "SourceForge Acquisition and Future Plans | SourceForge Community Blog". sourceforge.net. 10 February 2016. Retrieved 2016-07-29.
- ↑ "SourceForge and Slashdot Have Been Sold | FOSS Force". 2016-01-29. Retrieved 2016-07-29.
- ↑ Sharwood, Simon (November 8, 2013). "GIMP flees SourceForge over dodgy ads and installer". The Register. Retrieved November 21, 2013.
- ↑ "SourceForge locked in projects of fleeing users, cashed in on malvertising". Ars Technica. Retrieved 2 June 2015.
- 1 2 "Sourceforge Hijacks the Nmap Sourceforge Account". Seclists.org. 3 June 2015.
- 1 2 Sean Gallagher (4 June 2015). "Black "mirror": SourceForge has now seized Nmap audit tool project". Ars Technica.
- ↑ "SourceForge grabs GIMP for Windows' account, wraps installer in bundle-pushing adware [Updated]" . Retrieved 2015-05-30.
- ↑ "These companies that mislead our users". 7 Jul 2011.
- ↑ "VLC media player suffering in face of crapware and uncaring Google". Geek.com. 7 Jul 2011. Archived from the original on 23 March 2017. Retrieved 3 June 2015.
- ↑ "VideoLAN Calls Out for Help to Protect Users from VLC Scams". 16 Jul 2011.
- ↑ "Adware in new installer". The VideoLAN forums.