Related Research Articles
The Internet Control Message Protocol (ICMP) is a supporting protocol in the Internet protocol suite. It is used by network devices, including routers, to send error messages and operational information indicating success or failure when communicating with another IP address, for example, an error is indicated when a requested service is not available or that a host or router could not be reached. ICMP differs from transport protocols such as TCP and UDP in that it is not typically used to exchange data between systems, nor is it regularly employed by end-user network applications.

ping is a computer network administration software utility used to test the reachability of a host on an Internet Protocol (IP) network. It is available for virtually all operating systems that have networking capability, including most embedded network administration software.

In computing, a denial-of-service attack is a cyber-attack in which the perpetrator seeks to make a machine or network resource unavailable to its intended users by temporarily or indefinitely disrupting services of a host connected to a network. Denial of service is typically accomplished by flooding the targeted machine or resource with superfluous requests in an attempt to overload systems and prevent some or all legitimate requests from being fulfilled. The range of attacks varies widely, spanning from inundating a server with millions of requests to slow its performance, overwhelming a server with a substantial amount of invalid data, to submitting requests with an illegitimate IP address.

In computer networking, IP address spoofing or IP spoofing is the creation of Internet Protocol (IP) packets with a false source IP address, for the purpose of impersonating another computing system.
The Address Resolution Protocol (ARP) is a communication protocol used for discovering the link layer address, such as a MAC address, associated with a given internet layer address, typically an IPv4 address. This mapping is a critical function in the Internet protocol suite. ARP was defined in 1982 by RFC 826, which is Internet Standard STD 37.

A SYN flood is a form of denial-of-service attack on data communications in which an attacker rapidly initiates a connection to a server without finalizing the connection. The server has to spend resources waiting for half-opened connections, which can consume enough resources to make the system unresponsive to legitimate traffic.
The Internet Group Management Protocol (IGMP) is a communications protocol used by hosts and adjacent routers on IPv4 networks to establish multicast group memberships. IGMP is an integral part of IP multicast and allows the network to direct multicast transmissions only to hosts that have requested them.
In computer networking, promiscuous mode is a mode for a wired network interface controller (NIC) or wireless network interface controller (WNIC) that causes the controller to pass all traffic it receives to the central processing unit (CPU) rather than passing only the frames that the controller is specifically programmed to receive. This mode is normally used for packet sniffing that takes place on a router or on a computer connected to a wired network or one being part of a wireless LAN. Interfaces are placed into promiscuous mode by software bridges often used with hardware virtualization.
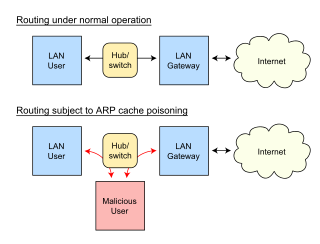
In computer networking, ARP spoofing, ARP cache poisoning, or ARP poison routing, is a technique by which an attacker sends (spoofed) Address Resolution Protocol (ARP) messages onto a local area network. Generally, the aim is to associate the attacker's MAC address with the IP address of another host, such as the default gateway, causing any traffic meant for that IP address to be sent to the attacker instead.
Distributed denial-of-service attacks on root nameservers are Internet events in which distributed denial-of-service attacks target one or more of the thirteen Domain Name System root nameserver clusters. The root nameservers are critical infrastructure components of the Internet, mapping domain names to IP addresses and other resource record (RR) data.
A ping of death is a type of attack on a computer system that involves sending a malformed or otherwise malicious ping to a computer. In this attack, a host sends hundreds of ping requests with a packet size that is large or illegal to another host to try to take it offline or to keep it preoccupied responding with ICMP Echo replies.
A ping flood is a simple denial-of-service attack where the attacker overwhelms the victim with ICMP "echo request" (ping) packets. This is most effective by using the flood option of ping which sends ICMP packets as fast as possible without waiting for replies. Most implementations of ping require the user to be privileged in order to specify the flood option. It is most successful if the attacker has more bandwidth than the victim. The attacker hopes that the victim will respond with ICMP "echo reply" packets, thus consuming both outgoing bandwidth as well as incoming bandwidth. If the target system is slow enough, it is possible to consume enough of its CPU cycles for a user to notice a significant slowdown.

In computer networking, telecommunication and information theory, broadcasting is a method of transferring a message to all recipients simultaneously. Broadcasting can be performed as a high-level operation in a program, for example, broadcasting in Message Passing Interface, or it may be a low-level networking operation, for example broadcasting on Ethernet.
In computer networking, ingress filtering is a technique used to ensure that incoming packets are actually from the networks from which they claim to originate. This can be used as a countermeasure against various spoofing attacks where the attacker's packets contain fake IP addresses. Spoofing is often used in denial-of-service attacks, and mitigating these is a primary application of ingress filtering.
A UDP flood attack is a volumetric denial-of-service (DoS) attack using the User Datagram Protocol (UDP), a sessionless/connectionless computer networking protocol.
arping is a computer software tool for discovering and probing hosts on a computer network. Arping probes hosts on the examined network link by sending link layer frames using the Address Resolution Protocol (ARP) request method addressed to a host identified by its MAC address of the network interface. The utility program may use ARP to resolve an IP address provided by the user.
In networking, a black hole, also known as a block hole, refers to a place in the network where incoming or outgoing traffic is silently discarded, without informing the source that the data did not reach its intended recipient.
An ICMP tunnel establishes a covert connection between two remote computers, using ICMP echo requests and reply packets. An example of this technique is tunneling complete TCP traffic over ping requests and replies.
A broadcast storm or broadcast radiation is the accumulation of broadcast and multicast traffic on a computer network. Extreme amounts of broadcast traffic constitute a broadcast storm. It can consume sufficient network resources so as to render the network unable to transport normal traffic. A packet that induces such a storm is occasionally nicknamed a Chernobyl packet.
The BlackNurse attack is a form of denial of service attack based on ICMP flooding. The attack is special because a modest bandwidth of 20Mbit/s can be effective for disrupting a victim's network.
References
- ↑ Sun, Fei Xian (2011). "Danger Theory Based Risk Evaluation Model for Smurf Attacks". Key Engineering Materials. 467–469: 515–521. doi:10.4028/www.scientific.net/KEM.467-469.515. ISSN 1662-9795. S2CID 110045205.
- ↑ "Tfreak". Hackepedia. 2013-03-28. Retrieved 2019-11-13.
- ↑ Pramatarov, Martin (2021-09-09). "What is a Smurf DDoS attack?". ClouDNS Blog. Retrieved 2022-09-15.
- ↑ For example, netscan.org (Web Archive) showed 122,945 broken networks as of Jan 25, 1999, but only 2,417 as of Jan 06, 2005.
- ↑ S. Kumar (5 July 2007). Kumar, Sanjeev (2007). "Smurf-based Distributed Denial of Service (DDoS) Attack Amplification in Internet". Second International Conference on Internet Monitoring and Protection (ICIMP 2007). p. 25. doi:10.1109/ICIMP.2007.42. ISBN 978-0-7695-2911-0. S2CID 14876546 . Retrieved 2020-12-30.
{{cite book}}:|website=ignored (help) - ↑ Hartanto, Sri (2023-07-30). Sri Hartanto. "The Impact of Smurf Attack on Web Server in Communication Network and its Preventions". International Journal of Sustainable Applied Sciences (IJSAS). 1 (1): 35–46. ISSN 3025-5597.
- ↑ D. Senie (August 1999). Changing the Default for Directed Broadcasts in Routers. Network Working Group. doi: 10.17487/RFC2644 . BCP 34. RFC 2644.Best Common Practice. Updates RFC 1812.
- ↑ Ferguson, P.; Senie, D. (May 2000). Network Ingress Filtering: Defeating Denial of Service Attacks which employ IP Source Address Spoofing. IETF. doi: 10.17487/RFC2827 . BCP 38. RFC 2827.Best Common Practice.
- ↑ "A Cisco Guide to Defending Against Distributed Denial of Service Attacks". Cisco. Retrieved 2019-09-26.
- ↑ Hendric, William (23 March 2016). "Fraggle attack".
- ↑ Anonymous (2003). Maximum Security. Sams Publishing. ISBN 978-0-672-32459-8.