Forensic accounting, forensic accountancy or financial forensics is the specialty practice area of accounting that investigates whether firms engage in financial reporting misconduct, or financial misconduct within the workplace by employees, officers or directors of the organization. Forensic accountants apply a range of skills and methods to determine whether there has been financial misconduct by the firm or its employees.
Data remanence is the residual representation of digital data that remains even after attempts have been made to remove or erase the data. This residue may result from data being left intact by a nominal file deletion operation, by reformatting of storage media that does not remove data previously written to the media, or through physical properties of the storage media that allow previously written data to be recovered. Data remanence may make inadvertent disclosure of sensitive information possible should the storage media be released into an uncontrolled environment.

Digital forensics is a branch of forensic science encompassing the recovery, investigation, examination, and analysis of material found in digital devices, often in relation to mobile devices and computer crime. The term "digital forensics" was originally used as a synonym for computer forensics but has expanded to cover investigation of all devices capable of storing digital data. With roots in the personal computing revolution of the late 1970s and early 1980s, the discipline evolved in a haphazard manner during the 1990s, and it was not until the early 21st century that national policies emerged.

Database forensics is a branch of digital forensic science relating to the forensic study of databases and their related metadata.

The Sleuth Kit (TSK) is a library and collection of Unix- and Windows-based utilities for extracting data from disk drives and other storage so as to facilitate the forensic analysis of computer systems. It forms the foundation for Autopsy, a better known tool that is essentially a graphical user interface to the command line utilities bundled with The Sleuth Kit.
Anti–computer forensics or counter-forensics are techniques used to obstruct forensic analysis.
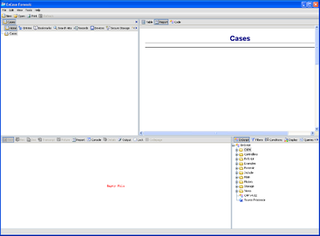
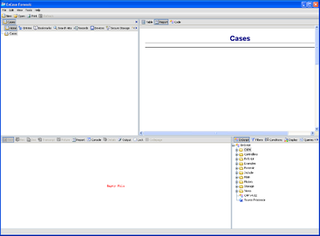
EnCase is the shared technology within a suite of digital investigations products by Guidance Software. The software comes in several products designed for forensic, cyber security, security analytics, and e-discovery use. EnCase is traditionally used in forensics to recover evidence from seized hard drives. It allows the investigator to conduct in-depth analysis of user files to collect evidence such as documents, pictures, internet history and Windows Registry information.
In computer security, a cold boot attack is a type of side channel attack in which an attacker with physical access to a computer performs a memory dump of a computer's random-access memory (RAM) by performing a hard reset of the target machine. Typically, cold boot attacks are used for retrieving encryption keys from a running operating system for malicious or criminal investigative reasons. The attack relies on the data remanence property of DRAM and SRAM to retrieve memory contents that remain readable in the seconds to minutes following a power switch-off.
Data erasure is a software-based method of data sanitization that aims to completely destroy all electronic data residing on a hard disk drive or other digital media by overwriting data onto all sectors of the device in an irreversible process. By overwriting the data on the storage device, the data is rendered irrecoverable.
Forensic Toolkit, or FTK, is a computer forensics software originally developed by AccessData, an Exterro company. It scans a hard drive looking for various information. It can, for example, potentially locate deleted emails and scan a disk for text strings to use them as a password dictionary to crack encryption.

Network forensics is a sub-branch of digital forensics relating to the monitoring and analysis of computer network traffic for the purposes of information gathering, legal evidence, or intrusion detection. Unlike other areas of digital forensics, network investigations deal with volatile and dynamic information. Network traffic is transmitted and then lost, so network forensics is often a pro-active investigation.
File carving is the process of reassembling computer files from fragments in the absence of filesystem metadata.

Mobile device forensics is a branch of digital forensics relating to recovery of digital evidence or data from a mobile device under forensically sound conditions. The phrase mobile device usually refers to mobile phones; however, it can also relate to any digital device that has both internal memory and communication ability, including PDA devices, GPS devices and tablet computers.

The digital forensic process is a recognized scientific and forensic process used in digital forensics investigations. Forensics researcher Eoghan Casey defines it as a number of steps from the original incident alert through to reporting of findings. The process is predominantly used in computer and mobile forensic investigations and consists of three steps: acquisition, analysis and reporting.
Guidance Software, Inc. was a public company founded in 1997. Headquartered in Pasadena, California, the company developed and provided software solutions for digital investigations primarily in the United States, Europe, the Middle East, Africa, and the Asia/Pacific Rim. Guidance Software had offices in Brazil, Chicago, Houston, New York City, San Francisco, Singapore, United Kingdom and Washington, D.C., and employed approximately 371 employees. On September 14, 2017, the company was acquired by OpenText.
Advanced Digital Forensic Solutions, Inc. is a company based in Reston, Virginia, that develops tools for scanning suspect computers and digital devices to locate and extract data, a process known as digital forensics. Digital forensic tools scan mobile phones, computers and digital devices to collect intelligence or evidence of a crime to identify computers that contain content relevant to an investigation.
Fileless malware is a variant of computer related malicious software that exists exclusively as a computer memory-based artifact i.e. in RAM. It does not write any part of its activity to the computer's hard drive, thus increasing its ability to evade antivirus software that incorporate file-based whitelisting, signature detection, hardware verification, pattern-analysis, time-stamping, etc., and leaving very little evidence that could be used by digital forensic investigators to identify illegitimate activity. Malware of this type is designed to work in memory, so its existence on the system lasts only until the system is rebooted.
William "Chuck" Easttom II is an American computer scientist specializing in cyber security, cryptography, quantum computing, and systems engineering.
This is a list of cybersecurity information technology. Cybersecurity is security as it is applied to information technology. This includes all technology that stores, manipulates, or moves data, such as computers, data networks, and all devices connected to or included in networks, such as routers and switches. All information technology devices and facilities need to be secured against intrusion, unauthorized use, and vandalism. Additionally, the users of information technology should be protected from theft of assets, extortion, identity theft, loss of privacy and confidentiality of personal information, malicious mischief, damage to equipment, business process compromise, and the general activity of cybercriminals. The public should be protected against acts of cyberterrorism, such as the compromise or loss of the electric power grid.