In physical security and information security, access control (AC) is the selective restriction of access to a place or other resource, while access management describes the process. The act of accessing may mean consuming, entering, or using. Permission to access a resource is called authorization.
An authenticator is a means used to confirm a user's identity, that is, to perform digital authentication. A person authenticates to a computer system or application by demonstrating that he or she has possession and control of an authenticator. In the simplest case, the authenticator is a common password.

A smart card, chip card, or integrated circuit card is a physical electronic authentication device, used to control access to a resource. It is typically a plastic credit card-sized card with an embedded integrated circuit (IC) chip. Many smart cards include a pattern of metal contacts to electrically connect to the internal chip. Others are contactless, and some are both. Smart cards can provide personal identification, authentication, data storage, and application processing. Applications include identification, financial, public transit, computer security, schools, and healthcare. Smart cards may provide strong security authentication for single sign-on (SSO) within organizations. Numerous nations have deployed smart cards throughout their populations.
RSA SecurID, formerly referred to as SecurID, is a mechanism developed by RSA for performing two-factor authentication for a user to a network resource.

A software protection dongle is an electronic copy protection and content protection device. When connected to a computer or other electronics, they unlock software functionality or decode content. The hardware key is programmed with a product key or other cryptographic protection mechanism and functions via an electrical connector to an external bus of the computer or appliance.

MIFARE is a series of integrated circuit (IC) chips used in contactless smart cards and proximity cards.
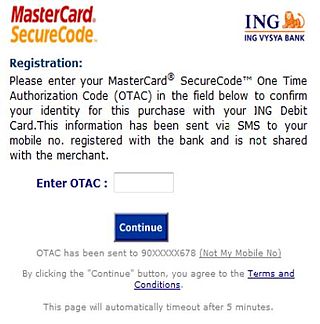
A one-time password (OTP), also known as a one-time PIN, one-time authorization code (OTAC) or dynamic password, is a password that is valid for only one login session or transaction, on a computer system or other digital device. OTPs avoid several shortcomings that are associated with traditional (static) password-based authentication; a number of implementations also incorporate two-factor authentication by ensuring that the one-time password requires access to something a person has as well as something a person knows.
Logical Security consists of software safeguards for an organization’s systems, including user identification and password access, authenticating, access rights and authority levels. These measures are to ensure that only authorized users are able to perform actions or access information in a network or a workstation. It is a subset of computer security.
Java Card is a software technology that allows Java-based applications (applets) to be run securely on smart cards and more generally on similar secure small memory footprint devices which are called "secure elements" (SE). Today, a Secure Element is not limited to its smart cards and other removable cryptographic tokens form factors; embedded SEs soldered onto a device board and new security designs embedded into general purpose chips are also widely used. Java Card addresses this hardware fragmentation and specificities while retaining code portability brought forward by Java.
HMAC-based one-time password (HOTP) is a one-time password (OTP) algorithm based on HMAC. It is a cornerstone of the Initiative for Open Authentication (OATH).
In Microsoft Windows, a Cryptographic Service Provider (CSP) is a software library that implements the Microsoft CryptoAPI (CAPI). CSPs implement encoding and decoding functions, which computer application programs may use, for example, to implement strong user authentication or for secure email.

A hardware security module (HSM) is a physical computing device that safeguards and manages secrets, performs encryption and decryption functions for digital signatures, strong authentication and other cryptographic functions. These modules traditionally come in the form of a plug-in card or an external device that attaches directly to a computer or network server. A hardware security module contains one or more secure cryptoprocessor chips.
There are a number of security and safety features new to Windows Vista, most of which are not available in any prior Microsoft Windows operating system release.

Multi-factor authentication is an electronic authentication method in which a user is granted access to a website or application only after successfully presenting two or more pieces of evidence to an authentication mechanism. MFA protects personal data—which may include personal identification or financial assets—from being accessed by an unauthorized third party that may have been able to discover, for example, a single password.

multiOTP is an open source PHP class, a command line tool, and a web interface that can be used to provide an operating-system-independent, strong authentication system. multiOTP is OATH-certified since version 4.1.0 and is developed under the LGPL license. Starting with version 4.3.2.5, multiOTP open source is also available as a virtual appliance - as a standard OVA file, a customized OVA file with open-vm-tools, and also as a Hyper-V downloadable file.

The FIDOAlliance is an open industry association launched in February 2013 whose stated mission is to develop and promote authentication standards that "help reduce the world’s over-reliance on passwords". FIDO addresses the lack of interoperability among devices that use strong authentication and reduces the problems users face creating and remembering multiple usernames and passwords.

The YubiKey is a hardware authentication device manufactured by Yubico to protect access to computers, networks, and online services that supports one-time passwords (OTP), public-key cryptography, and authentication, and the Universal 2nd Factor (U2F) and FIDO2 protocols developed by the FIDO Alliance. It allows users to securely log into their accounts by emitting one-time passwords or using a FIDO-based public/private key pair generated by the device. YubiKey also allows for storing static passwords for use at sites that do not support one-time passwords. Google, Amazon, Microsoft, Twitter, and Facebook use YubiKey devices to secure employee accounts as well as end user accounts. Some password managers support YubiKey. Yubico also manufactures the Security Key, a similar lower cost device with only FIDO2/WebAuthn and FIDO/U2F support.
Nitrokey is an open-source USB key used to enable the secure encryption and signing of data. The secret keys are always stored inside the Nitrokey which protects against malware and attackers. A user-chosen PIN and a tamper-proof smart card protect the Nitrokey in case of loss and theft. The hardware and software of Nitrokey are open-source. The free software and open hardware enables independent parties to verify the security of the device. Nitrokey is supported on Microsoft Windows, macOS, Linux, and BSD.
Biometric tokenization is the process of substituting a stored biometric template with a non-sensitive equivalent, called a token, that lacks extrinsic or exploitable meaning or value. The process combines the biometrics with public-key cryptography to enable the use of a stored biometric template for secure or strong authentication to applications or other systems without presenting the template in its original, replicable form.
Passwordless authentication is an authentication method in which a user can log in to a computer system without the entering a password or any other knowledge-based secret. In most common implementations users are asked to enter their public identifier and then complete the authentication process by providing a secure proof of identity through a registered device or token.