Related Research Articles

A password, sometimes called a passcode, is secret data, typically a string of characters, usually used to confirm a user's identity. Traditionally, passwords were expected to be memorized, but the large number of password-protected services that a typical individual accesses can make memorization of unique passwords for each service impractical. Using the terminology of the NIST Digital Identity Guidelines, the secret is held by a party called the claimant while the party verifying the identity of the claimant is called the verifier. When the claimant successfully demonstrates knowledge of the password to the verifier through an established authentication protocol, the verifier is able to infer the claimant's identity.
In computing, the Challenge-Handshake Authentication Protocol (CHAP) is an authentication protocol originally used by Point-to-Point Protocol (PPP) to validate users. CHAP is also carried in other authentication protocols such as RADIUS and Diameter.
In computer security, challenge–response authentication is a family of protocols in which one party presents a question ("challenge") and another party must provide a valid answer ("response") to be authenticated.

A cryptographic hash function (CHF) is a hash algorithm that has special properties desirable for a cryptographic application:

In cryptography, a key derivation function (KDF) is a cryptographic algorithm that derives one or more secret keys from a secret value such as a master key, a password, or a passphrase using a pseudorandom function. KDFs can be used to stretch keys into longer keys or to obtain keys of a required format, such as converting a group element that is the result of a Diffie–Hellman key exchange into a symmetric key for use with AES. Keyed cryptographic hash functions are popular examples of pseudorandom functions used for key derivation.
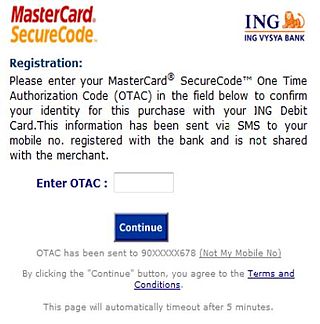
A one-time password (OTP), also known as a one-time PIN, one-time authorization code (OTAC) or dynamic password, is a password that is valid for only one login session or transaction, on a computer system or other digital device. OTPs avoid several shortcomings that are associated with traditional (static) password-based authentication; a number of implementations also incorporate two-factor authentication by ensuring that the one-time password requires access to something a person has as well as something a person knows.

A security token is a peripheral device used to gain access to an electronically restricted resource. The token is used in addition to, or in place of, a password. It acts like an electronic key to access something. Examples of security tokens include wireless keycards used to open locked doors, or a banking token used as a digital authenticator for signing in to online banking, or signing a transaction such as a wire transfer.
Self-service password reset (SSPR) is defined as any process or technology that allows users who have either forgotten their password or triggered an intruder lockout to authenticate with an alternate factor, and repair their own problem, without calling the help desk. It is a common feature in identity management software and often bundled in the same software package as a password synchronization capability.
In computer security, shoulder surfing is a type of social engineering technique used to obtain information such as personal identification numbers (PINs), passwords and other confidential data by looking over the victim's shoulder. Unauthorized users watch the keystrokes inputted on a device or listen to sensitive information being spoken, which is also known as eavesdropping.
In a Windows network, NT LAN Manager (NTLM) is a suite of Microsoft security protocols intended to provide authentication, integrity, and confidentiality to users. NTLM is the successor to the authentication protocol in Microsoft LAN Manager (LANMAN), an older Microsoft product. The NTLM protocol suite is implemented in a Security Support Provider, which combines the LAN Manager authentication protocol, NTLMv1, NTLMv2 and NTLM2 Session protocols in a single package. Whether these protocols are used or can be used on a system which is governed by Group Policy settings, for which different versions of Windows have different default settings.

Password strength is a measure of the effectiveness of a password against guessing or brute-force attacks. In its usual form, it estimates how many trials an attacker who does not have direct access to the password would need, on average, to guess it correctly. The strength of a password is a function of length, complexity, and unpredictability.
Electronic authentication is the process of establishing confidence in user identities electronically presented to an information system. Digital authentication, or e-authentication, may be used synonymously when referring to the authentication process that confirms or certifies a person's identity and works. When used in conjunction with an electronic signature, it can provide evidence of whether data received has been tampered with after being signed by its original sender. Electronic authentication can reduce the risk of fraud and identity theft by verifying that a person is who they say they are when performing transactions online.
OTPW is a one-time password system developed for authentication in Unix-like operating systems by Markus Kuhn. A user's real password is not directly transmitted across the network. Rather, a series of one-time passwords is created from a short set of characters and a set of one-time tokens. As each single-use password can only be used once, passwords intercepted by a password sniffer or key logger are not useful to an attacker.
Draw a Secret (DAS) is a graphical password input scheme developed by Ian Jermyn, Alain Mayer, Fabian Monrose, Michael K. Reiter and Aviel D. Rubin and presented in a paper at the 8th USENIX Security Symposium in Augusts 1999.
Multi-factor authentication is an electronic authentication method in which a user is granted access to a website or application only after successfully presenting two or more pieces of evidence to an authentication mechanism. MFA protects personal data—which may include personal identification or financial assets—from being accessed by an unauthorized third party that may have been able to discover, for example, a single password.
A cognitive password is a form of knowledge-based authentication that requires a user to answer a question, presumably something they intrinsically know, to verify their identity. Cognitive password systems have been researched for many years and are currently commonly used as a form of secondary access. They were developed to overcome the common memorability vs. strength problem that exists with the traditional password. Cognitive passwords, when compared to other password systems, can be measured through the usage of a memorability vs. guessability ratio.

Google Authenticator is a software-based authenticator by Google. It implements multi-factor authentication services using the time-based one-time password and HMAC-based one-time password, for authenticating users of software applications.
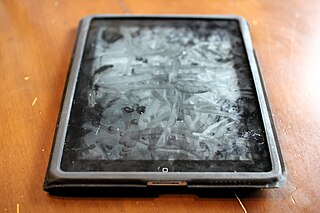
A smudge attack is an information extraction attack that discerns the password input of a touchscreen device such as a cell phone or tablet computer from fingerprint smudges. A team of researchers at the University of Pennsylvania were the first to investigate this type of attack in 2010. An attack occurs when an unauthorized user is in possession or is nearby the device of interest. The attacker relies on detecting the oily smudges produced and left behind by the user's fingers to find the pattern or code needed to access the device and its contents. Simple cameras, lights, fingerprint powder, and image processing software can be used to capture the fingerprint deposits created when the user unlocks their device. Under proper lighting and camera settings, the finger smudges can be easily detected, and the heaviest smudges can be used to infer the most frequent input swipes or taps from the user.
PassMap is a map-based graphical password method of authentication, similar to passwords, proposed by National Tsing Hua University researchers. The word PassMap originates from the word password by substituting word with map.

A thermal attack is an approach that exploits heat traces to uncover the entered credentials. These attacks rely on the phenomenon of heat transfer from one object to another. During authentication, heat transfers from the users' hands to the surface they are interacting with, leaving heat traces behind that can be analyzed using thermal cameras that operate in the far-infrared spectrum. These traces can be recovered and used to reconstruct the passwords. In some cases, the attack can be successful even 30 seconds after the user has authenticated.
References
- ↑ graphical password or graphical user authentication (GUA). searchsecurity.techtarget.com. Retrieved on 2012-05-20.
- ↑ Ericka Chickowski (2010-11-03). "Images Could Change the Authentication Picture". Dark Reading.
- ↑ "Confident Technologies Delivers Image-Based, Multifactor Authentication to Strengthen Passwords on Public-Facing Websites"> "Confident Technologies Delivers Image-Based, Multifactor Authentication to Strengthen Passwords on Public-Facing Websites". 2010-10-28.
- ↑ Butler, Rick A. (2004-12-21) Face in the Crowd. mcpmag.com. Retrieved on 2012-05-20.
- ↑ Oorschot, P. C. van; Thorpe, Julie (January 2008). "On predictive models and user-drawn graphical passwords". ACM Transactions on Information and System Security. 10 (4): 1–33. CiteSeerX 10.1.1.216.5451 . doi:10.1145/1284680.1284685. ISSN 1094-9224. S2CID 3849996.
- ↑ Zakaria, Nur Haryani; Griffiths, David; Brostoff, Sacha; Yan, Jeff (20 July 2011). "Shoulder Surfing Defence for Recall-based Graphical Passwords" (PDF). Symposium On Usable Privacy and Security (SOUPS) 2011.