
A COM file is a type of simple executable file. On the Digital Equipment Corporation (DEC) VAX operating systems of the 1970s, .COM was used as a filename extension for text files containing commands to be issued to the operating system. With the introduction of Digital Research's CP/M, the type of files commonly associated with COM extension changed to that of executable files. This convention was later carried over to DOS. Even when complemented by the more general EXE file format for executables, the compact COM files remained viable and frequently used under DOS.
Abraxas, also known as Abraxas5, discovered in April 1993, is an encrypted, overwriting, file infecting computer virus which infects .COM and .EXE files, although it does not infect command.com. It does not become memory resident. Each time an infected file is executed, Abraxas infects the copy of dosshell.com located in the C:\DOS directory, as well as one EXE file in the current directory. Due to a bug in the virus, only the first EXE file in any directory is infected.
Acid is a computer virus which infects .COM and .EXE files including command.com. Each time an infected file is executed, Acid infects all of the .EXE files in the current directory. Later, if an infected file is executed, it infects the .COM files in the current directory. Programs infected with Acid will have had the first 792 bytes of the host program overwritten with Acid's own code. There will be no file length increase unless the original host program was smaller than 792 bytes, in which case it will become 792 bytes in length. The program's date and time in the DOS disk directory listing will not be altered.
Acme is a computer virus which infects MS-DOS EXE files. Each time an infected file is executed, Acme may infect an EXE in the current directory by creating a hidden 247 byte long read-only COM file with the same base name. Acme is a variant of Clonewar, a spawning virus. Acme is also perhaps a descendant of the small single-step infector Zeno, which is not to be confused with the Zeno programming language.
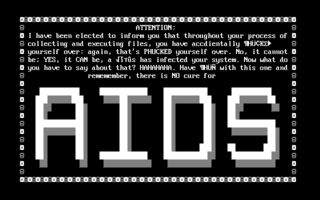
AIDS is a DOS computer virus which overwrites COM files.
ABC, discovered in October 1992, is a memory-resident, file-infecting computer virus which infects EXE files and may alter both COM and EXE files. ABC activates on the 13th day of every month.
Jerusalem is a logic bomb DOS virus first detected at Hebrew University of Jerusalem, in October 1987. On infection, the Jerusalem virus becomes memory resident, and then infects every executable file run, except for COMMAND.COM. COM files grow by 1,813 bytes when infected by Jerusalem and are not re-infected. Executable files grow by 1,808 to 1,823 bytes each time they are infected, and are then re-infected each time the files are loaded until they are too large to load into memory. Some .EXE files are infected but do not grow because several overlays follow the genuine .EXE file in the same file. Sometimes .EXE files are incorrectly infected, causing the program to fail to run as soon as it is executed.
Scott's Valley [sic] is a computer virus, a member of the Slow virus family and distantly related to the Jerusalem virus family. It was discovered in September 1990 in Scotts Valley, California.
Sunday is a computer virus, a member of the Jerusalem virus family. It was discovered in November 1989 after a number of simultaneous reports from Seattle, Washington, United States, and surrounding areas. Several other Seattle outbreaks, including AirCop, were later traced to Asia.
Alabama is a computer virus, discovered in October 1989 on the campus of the Hebrew University of Jerusalem.
Ontario is a family of computer viruses, named after its point of isolation, the Canadian province of Ontario. This family of computer virus consists of Ontario.1024, Ontario.512 and Ontario.2048. The first variant Ontario.512 was discovered in July 1990. Because Ontario.1024 was also discovered in Ontario, it is likely that both viruses originate from within the province. By the Ontario.2048 variant, the author had adopted "Ontario" as the family's name and even included the name "Ontario-3" in the virus code.
Bomber is a DOS polymorphic memory resident computer virus, known for its technique of "patchy infection". This method of infection is very similar to that which is utilised by the OneHalf computer virus.
CTX is a computer virus created in Spain in 1999. CTX was initially discovered as part of the Cholera worm, with which the author intentionally infected with CTX. Although the Cholera worm had the capability to send itself via email, the CTX worm quickly surpassed it in prevalence. Cholera is now considered obsolete, while CTX remains in the field, albeit with only rare discoveries.

The Cascade virus is a prominent computer virus that was a resident written in assembly language, that was widespread in the 1980s and early 1990s. It infected .COM files and had the effect of making text on the screen fall down and form a heap at the bottom of the screen. It was notable for using an encryption algorithm to avoid being detected. However, one could see that infected files had their size increased by 1701 or 1704 bytes. In response, IBM developed its own antivirus software.
5lo is a computer virus that increases file size and does little more than replicate. Size: 1,032 bytes
KoKo Virus is a memory resident computer virus created in March 1991. KoKo's name came from the creator himself, which was a nickname used by his friends. Many on-line virus databases refer to KoKo as Koko.1780. KoKo is written in the Assembly programming language and the executable file usually has an approximate file size of around 1780 bytes.

A computer virus is a type of malware that, when executed, replicates itself by modifying other computer programs and inserting its own code into those programs. If this replication succeeds, the affected areas are then said to be "infected" with a computer virus, a metaphor derived from biological viruses.
Daprosy worm was a malicious computer program that spreads via local area network (LAN) connections, spammed e-mails and USB mass storage devices. Infection comes from a single read1st.exe file where several dozen clones are created at once bearing the names of compromised folders. The most obvious symptom of Daprosy infection is the presence of Classified.exe or Do not open - secrets!.exe files from infected folders.
Sality is the classification for a family of malicious software (malware), which infects Microsoft Windows systems files. Sality was first discovered in 2003 and has advanced to become a dynamic, enduring and full-featured form of malicious code. Systems infected with Sality may communicate over a peer-to-peer (P2P) network to form a botnet to relay spam, proxying of communications, exfiltrating sensitive data, compromising web servers and/or coordinating distributed computing tasks to process intensive tasks. Since 2010, certain variants of Sality have also incorporated rootkit functions as part of an ongoing evolution of the malware family. Because of its continued development and capabilities, Sality is considered one of the most complex and formidable forms of malware to date.
Win32/Patched is a computer Trojan targeting the Microsoft Windows operating system that was first detected in October 2008. Files detected as "Trojan.Win32.Patched" are usually Windows components that are patched by a malicious application. The purpose of patching varies. For example, certain malware patches system components in order to disable security, such as the Windows Safe File Check feature. Other malware can add parts of its code to a system component and then patch certain functions of the original file to point to an appended code.