| General | |
|---|---|
| Designers | Ingrid Schaumuller-Bichl |
| First published | 1981 |
| Derived from | DES |
| Cipher detail | |
| Block sizes | variable, multiple of 32 |
| Structure | generalized Feistel network |
| Rounds | variable, even |
| Best public cryptanalysis | |
| differential cryptanalysis breaks most variants more easily than DES | |
In cryptography, the Generalized DES Scheme (GDES or G-DES) is a variant of the DES symmetric-key block cipher designed with the intention of speeding up the encryption process while improving its security. The scheme was proposed by Ingrid Schaumuller-Bichl in 1981.

Cryptography or cryptology is the practice and study of techniques for secure communication in the presence of third parties called adversaries. More generally, cryptography is about constructing and analyzing protocols that prevent third parties or the public from reading private messages; various aspects in information security such as data confidentiality, data integrity, authentication, and non-repudiation are central to modern cryptography. Modern cryptography exists at the intersection of the disciplines of mathematics, computer science, electrical engineering, communication science, and physics. Applications of cryptography include electronic commerce, chip-based payment cards, digital currencies, computer passwords, and military communications.

The Data Encryption Standard is a symmetric-key algorithm for the encryption of electronic data. Although its short key length of 56 bits, criticized from the beginning, makes it too insecure for most current applications, it was highly influential in the advancement of modern cryptography.
Symmetric-key algorithms are algorithms for cryptography that use the same cryptographic keys for both encryption of plaintext and decryption of ciphertext. The keys may be identical or there may be a simple transformation to go between the two keys. The keys, in practice, represent a shared secret between two or more parties that can be used to maintain a private information link. This requirement that both parties have access to the secret key is one of the main drawbacks of symmetric key encryption, in comparison to public-key encryption.
In 1990, Eli Biham and Adi Shamir showed that GDES was vulnerable to differential cryptanalysis, and that any GDES variant faster than DES is also less secure than DES.

Eli Biham is an Israeli cryptographer and cryptanalyst, currently a professor at the Technion Israeli Institute of Technology Computer Science department. Starting from October 2008 and till 2013, Biham was the dean of the Technion Computer Science department, after serving for two years as chief of CS graduate school. Biham received his Ph.D. for inventing (publicly) differential cryptanalysis, while working under Adi Shamir. It had, it turned out, been invented at least twice before. A team at IBM discovered it during their work on DES, and was requested/required to keep their discovery secret by the NSA, who evidently knew about it as well.

Adi Shamir is an Israeli cryptographer. He is a co-inventor of the Rivest–Shamir–Adleman (RSA) algorithm, a co-inventor of the Feige–Fiat–Shamir identification scheme, one of the inventors of differential cryptanalysis and has made numerous contributions to the fields of cryptography and computer science.
Differential cryptanalysis is a general form of cryptanalysis applicable primarily to block ciphers, but also to stream ciphers and cryptographic hash functions. In the broadest sense, it is the study of how differences in information input can affect the resultant difference at the output. In the case of a block cipher, it refers to a set of techniques for tracing differences through the network of transformation, discovering where the cipher exhibits non-random behavior, and exploiting such properties to recover the secret key.
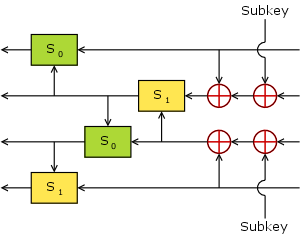
GDES generalizes the Feistel network structure of DES to larger block sizes. In each round, the DES round function is applied to the rightmost 32-bit subblock, and the result is XORed with all the other parts. Then the block is rotated 32 bits to the right.
In cryptography, a Feistel cipher is a symmetric structure used in the construction of block ciphers, named after the German-born physicist and cryptographer Horst Feistel who did pioneering research while working for IBM (USA); it is also commonly known as a Feistel network. A large proportion of block ciphers use the scheme, including the Data Encryption Standard (DES). The Feistel structure has the advantage that encryption and decryption operations are very similar, even identical in some cases, requiring only a reversal of the key schedule. Therefore, the size of the code or circuitry required to implement such a cipher is nearly halved.
In modern cryptography, symmetric key ciphers are generally divided into stream ciphers and block ciphers. Block ciphers operate on a fixed length string of bits. The length of this bit string is the block size. Both the input (plaintext) and output (ciphertext) are the same length; the output cannot be shorter than the input – this follows logically from the pigeonhole principle and the fact that the cipher must be reversible – and it is undesirable for the output to be longer than the input.