A password, sometimes called a passcode, is secret data, typically a string of characters, usually used to confirm a user's identity. Traditionally, passwords were expected to be memorized, but the large number of password-protected services that a typical individual accesses can make memorization of unique passwords for each service impractical. Using the terminology of the NIST Digital Identity Guidelines, the secret is held by a party called the claimant while the party verifying the identity of the claimant is called the verifier. When the claimant successfully demonstrates knowledge of the password to the verifier through an established authentication protocol, the verifier is able to infer the claimant's identity.
A personal identification number (PIN), PIN code, or sometimes redundantly a PIN number, is a numeric passcode used in the process of authenticating a user accessing a system.

In cryptography, a key derivation function (KDF) is a cryptographic algorithm that derives one or more secret keys from a secret value such as a master key, a password, or a passphrase using a pseudorandom function. KDFs can be used to stretch keys into longer keys or to obtain keys of a required format, such as converting a group element that is the result of a Diffie–Hellman key exchange into a symmetric key for use with AES. Keyed cryptographic hash functions are popular examples of pseudorandom functions used for key derivation.
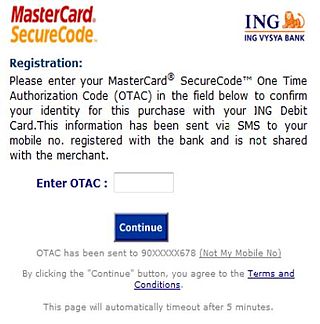
A one-time password (OTP), also known as a one-time PIN, one-time authorization code (OTAC) or dynamic password, is a password that is valid for only one login session or transaction, on a computer system or other digital device. OTPs avoid several shortcomings that are associated with traditional (static) password-based authentication; a number of implementations also incorporate two-factor authentication by ensuring that the one-time password requires access to something a person has as well as something a person knows.
A password policy is a set of rules designed to enhance computer security by encouraging users to employ strong passwords and use them properly. A password policy is often part of an organization's official regulations and may be taught as part of security awareness training. Either the password policy is merely advisory, or the computer systems force users to comply with it. Some governments have national authentication frameworks that define requirements for user authentication to government services, including requirements for passwords.
Account aggregation sometimes also known as financial data aggregation is a method that involves compiling information from different accounts, which may include bank accounts, credit card, payroll accounts, investment accounts, and other consumer or business accounts, into a single place. This may be provided through connecting via an API to the financial institution or provided through "screen scraping" where a user provides the requisite account-access information for an automated system to gather and compile the information into a single page. The security of the account access details as well as the financial information is key to users having confidence in the service.
Self-service password reset (SSPR) is defined as any process or technology that allows users who have either forgotten their password or triggered an intruder lockout to authenticate with an alternate factor, and repair their own problem, without calling the help desk. It is a common feature in identity management software and often bundled in the same software package as a password synchronization capability.
3-D Secure is a protocol designed to be an additional security layer for online credit and debit card transactions. The name refers to the "three domains" which interact using the protocol: the merchant/acquirer domain, the issuer domain, and the interoperability domain.

Password strength is a measure of the effectiveness of a password against guessing or brute-force attacks. In its usual form, it estimates how many trials an attacker who does not have direct access to the password would need, on average, to guess it correctly. The strength of a password is a function of length, complexity, and unpredictability.
A password manager is a computer program that allows users to store and manage their passwords for local applications or online services such as web applications, online shops or social media. A web browser generally has a built in version of a password manager. These have been criticized frequently as many have stored the passwords in plaintext, allowing hacking attempts.
Data Protection Application Programming Interface (DPAPI) is a simple cryptographic application programming interface available as a built-in component in Windows 2000 and later versions of Microsoft Windows operating systems. In theory, the Data Protection API can enable symmetric encryption of any kind of data; in practice, its primary use in the Windows operating system is to perform symmetric encryption of asymmetric private keys, using a user or system secret as a significant contribution of entropy. A detailed analysis of DPAPI inner-workings was published in 2011 by Bursztein et al.
Electronic authentication is the process of establishing confidence in user identities electronically presented to an information system. Digital authentication, or e-authentication, may be used synonymously when referring to the authentication process that confirms or certifies a person's identity and works. When used in conjunction with an electronic signature, it can provide evidence of whether data received has been tampered with after being signed by its original sender. Electronic authentication can reduce the risk of fraud and identity theft by verifying that a person is who they say they are when performing transactions online.

Multi-factor authentication is an electronic authentication method in which a user is granted access to a website or application only after successfully presenting two or more pieces of evidence to an authentication mechanism. MFA protects personal data—which may include personal identification or financial assets—from being accessed by an unauthorized third party that may have been able to discover, for example, a single password.
Knowledge-based authentication, commonly referred to as KBA, is a method of authentication which seeks to prove the identity of someone accessing a service such as a financial institution or website. As the name suggests, KBA requires the knowledge of private information from the individual to prove that the person providing the identity information is the owner of the identity. There are two types of KBA: static KBA, which is based on a pre-agreed set of shared secrets, and dynamic KBA, which is based on questions generated from a wider base of personal information.
A cognitive password is a form of knowledge-based authentication that requires a user to answer a question, presumably something they intrinsically know, to verify their identity. Cognitive password systems have been researched for many years and are currently commonly used as a form of secondary access. They were developed to overcome the common memorability vs. strength problem that exists with the traditional password. Cognitive passwords, when compared to other password systems, can be measured through the usage of a memorability vs. guessability ratio.
Apple Account, formerly known as Apple ID, is a user account by Apple for their devices and software. Apple Accounts contain the user's personal data and settings, and when an Apple Account is used to log in to an Apple device, the device will automatically use the data and settings associated with the Apple Account.

Elie Bursztein, is a French computer scientist and software engineer. He is Google and DeepMind AI cybersecurity technical and research lead.

A Microsoft account or MSA is a single sign-on personal user account for Microsoft customers to log in to consumer Microsoft services, devices running on one of Microsoft's current operating systems, and Microsoft application software.

Google Authenticator is a software-based authenticator by Google. It implements multi-factor authentication services using the time-based one-time password and HMAC-based one-time password, for authenticating users of software applications.
Credential stuffing is a type of cyberattack in which the attacker collects stolen account credentials, typically consisting of lists of usernames or email addresses and the corresponding passwords, and then uses the credentials to gain unauthorized access to user accounts on other systems through large-scale automated login requests directed against a web application. Unlike credential cracking, credential stuffing attacks do not attempt to use brute force or guess any passwords – the attacker simply automates the logins for a large number of previously discovered credential pairs using standard web automation tools such as Selenium, cURL, PhantomJS or tools designed specifically for these types of attacks, such as Sentry MBA, SNIPR, STORM, Blackbullet and Openbullet.