Related Research Articles
In communications and information processing, code is a system of rules to convert information—such as a letter, word, sound, image, or gesture—into another form, sometimes shortened or secret, for communication through a communication channel or storage in a storage medium. An early example is an invention of language, which enabled a person, through speech, to communicate what they thought, saw, heard, or felt to others. But speech limits the range of communication to the distance a voice can carry and limits the audience to those present when the speech is uttered. The invention of writing, which converted spoken language into visual symbols, extended the range of communication across space and time.
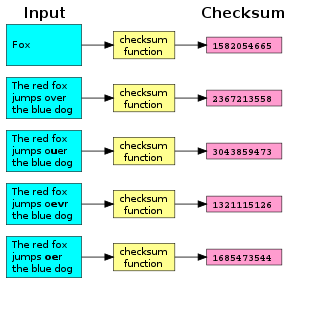
A checksum is a small-sized block of data derived from another block of digital data for the purpose of detecting errors that may have been introduced during its transmission or storage. By themselves, checksums are often used to verify data integrity but are not relied upon to verify data authenticity.
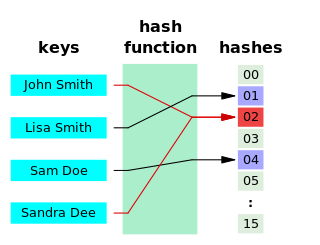
A hash function is any function that can be used to map data of arbitrary size to fixed-size values, though there are some hash functions that support variable length output. The values returned by a hash function are called hash values, hash codes, digests, or simply hashes. The values are usually used to index a fixed-size table called a hash table. Use of a hash function to index a hash table is called hashing or scatter storage addressing.
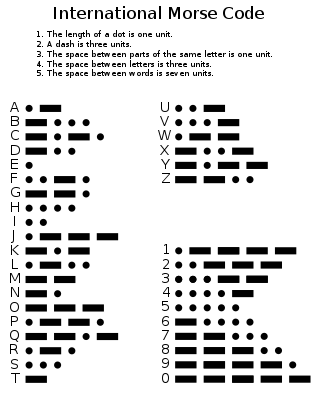
Morse code is a method used in telecommunication to encode text characters as standardized sequences of two different signal durations, called dots and dashes, or dits and dahs. Morse code is named after Samuel Morse, one of the early developers of the system adopted for electrical telegraphy.
V, or v, is the 22nd letter in the Latin alphabet, used in the modern English alphabet, the alphabets of other western European languages and others worldwide. Its name in English is vee, plural vees.

The (International) Radiotelephony Spelling Alphabet, commonly known as the NATO phonetic alphabet, is the most widely used set of clear code words for communicating the letters of the Roman alphabet. Technically a radiotelephonic spelling alphabet, it goes by various names, including NATO spelling alphabet, ICAO phonetic alphabet and ICAO spelling alphabet. The ITU phonetic alphabet and figure code is a rarely used variant that differs in the code words for digits.
A passphrase is a sequence of words or other text used to control access to a computer system, program or data. It is similar to a password in usage, but a passphrase is generally longer for added security. Passphrases are often used to control both access to, and the operation of, cryptographic programs and systems, especially those that derive an encryption key from a passphrase. The origin of the term is by analogy with password. The modern concept of passphrases is believed to have been invented by Sigmund N. Porter in 1982.
In computer programming, Base64 is a group of tetrasexagesimal binary-to-text encoding schemes that represent binary data in sequences of 24 bits that can be represented by four 6-bit Base64 digits.
In telecommunications, 8b/10b is a line code that maps 8-bit words to 10-bit symbols to achieve DC balance and bounded disparity, and at the same time provide enough state changes to allow reasonable clock recovery. This means that the difference between the counts of ones and zeros in a string of at least 20 bits is no more than two, and that there are not more than five ones or zeros in a row. This helps to reduce the demand for the lower bandwidth limit of the channel necessary to transfer the signal.
Base32 is an encoding method based on the base-32 numeral system. It uses an alphabet of 32 digits, each of which represents a different combination of 5 bits (25). Since base32 is not very widely adopted, the question of notation—which characters to use to represent the 32 digits—is not as settled as in the case of more well-known numeral systems (such as hexadecimal), though RFCs and unofficial and de-facto standards exist. One way to represent Base32 numbers in a human-readable way is by using the digits 0–9 and the twenty-two upper-case letters A–V. However, many other variations are used in different contexts. Historically, Baudot code could be considered a modified (stateful) base32 code.

Diceware is a method for creating passphrases, passwords, and other cryptographic variables using ordinary dice as a hardware random number generator. For each word in the passphrase, five rolls of a six-sided die are required. The numbers from 1 to 6 that come up in the rolls are assembled as a five-digit number, e.g. 43146. That number is then used to look up a word in a cryptographic word list. In the original Diceware list 43146 corresponds to munch. By generating several words in sequence, a lengthy passphrase can thus be constructed randomly.
PGPfone was a secure voice telephony system developed by Philip Zimmermann in 1995. The PGPfone protocol had little in common with Zimmermann's popular PGP email encryption package, except for the use of the name. It used ephemeral Diffie-Hellman protocol to establish a session key, which was then used to encrypt the stream of voice packets. The two parties compared a short authentication string to detect a Man-in-the-middle attack, which is the most common method of wiretapping secure phones of this type. PGPfone could be used point-to-point over the public switched telephone network, or over the Internet as an early Voice over IP system.
The diehard tests are a battery of statistical tests for measuring the quality of a random number generator. They were developed by George Marsaglia over several years and first published in 1995 on a CD-ROM of random numbers.
A binary-to-text encoding is encoding of data in plain text. More precisely, it is an encoding of binary data in a sequence of printable characters. These encodings are necessary for transmission of data when the communication channel does not allow binary data or is not 8-bit clean. PGP documentation uses the term "ASCII armor" for binary-to-text encoding when referring to Base64.
A spelling alphabet is a set of words used to represent the letters of an alphabet in oral communication, especially over a two-way radio or telephone. The words chosen to represent the letters sound sufficiently different from each other to clearly differentiate them. This avoids any confusion that could easily otherwise result from the names of letters that sound similar, except for some small difference easily missed or easily degraded by the imperfect sound quality of the apparatus. For example, in the Latin alphabet, the letters B, P, and D sound similar and could easily be confused, but the words "bravo", "papa" and "delta" sound completely different, making confusion unlikely.
In public-key cryptography, a public key fingerprint is a short sequence of bytes used to identify a longer public key. Fingerprints are created by applying a cryptographic hash function to a public key. Since fingerprints are shorter than the keys they refer to, they can be used to simplify certain key management tasks. In Microsoft software, "thumbprint" is used instead of "fingerprint."
The ISO basic Latin alphabet is an international standard for a Latin-script alphabet that consists of two sets of 26 letters, codified in various national and international standards and used widely in international communication. They are the same letters that comprise the current English alphabet. Since medieval times, they are also the same letters of the modern Latin alphabet. The order is also important for sorting words into alphabetical order.
The tie is a symbol in the shape of an arc similar to a large breve, used in Greek, phonetic alphabets, and Z notation. It can be used between two characters with spacing as punctuation, non-spacing as a diacritic, or (underneath) as a proofreading mark. It can be above or below, and reversed. Its forms are called tie, double breve, enotikon or papyrological hyphen, ligature tie, and undertie.
ZPAQ is an open source command line archiver for Windows and Linux. It uses a journaling or append-only format which can be rolled back to an earlier state to retrieve older versions of files and directories. It supports fast incremental update by adding only files whose last-modified date has changed since the previous update. It compresses using deduplication and several algorithms depending on the data type and the selected compression level. To preserve forward and backward compatibility between versions as the compression algorithm is improved, it stores the decompression algorithm in the archive. The ZPAQ source code includes a public domain API, libzpaq, which provides compression and decompression services to C++ applications. The format is believed to be unencumbered by patents.
References
- This article incorporates material that is copyrighted by PGP Corporation and has been licensed under the GNU Free Documentation License. (per Jon Callas, CTO, CSO PGP Corporation, 4-Jan-2007)
- ↑ Juola, Patrick; Zimmermann, Philip (1996). "Whole-word phonetic distances and the PGPfone alphabet" (PDF). Proceeding of Fourth International Conference on Spoken Language Processing. ICSLP '96. Vol. 1. pp. 98–101. doi:10.1109/ICSLP.1996.607046. ISBN 0-7803-3555-4. S2CID 10385500.
- ↑ Juola, Patrick (1996). "Isolated Word Confusion Metrics and the PGPfone Alphabet". Proceedings of New Methods in Language Processing 2. Ankara, Turkey: Oxford University, Dept. of Experimental Psychology. arXiv: cmp-lg/9608021 . Bibcode:1996cmp.lg....8021J.
- ↑ "Archived copy". web.mit.edu. Archived from the original on 26 March 2010. Retrieved 12 January 2022.
{{cite web}}: CS1 maint: archived copy as title (link) - ↑ "EFF's New Wordlists for Random Passphrases". 19 July 2016.
- ↑ mnemonic encoding Archived 2008-03-02 at the Wayback Machine and updated code