A wireless network is a computer network that uses wireless data connections between network nodes. Wireless networking allows homes, telecommunications networks and business installations to avoid the costly process of introducing cables into a building, or as a connection between various equipment locations. Admin telecommunications networks are generally implemented and administered using radio communication. This implementation takes place at the physical level (layer) of the OSI model network structure.
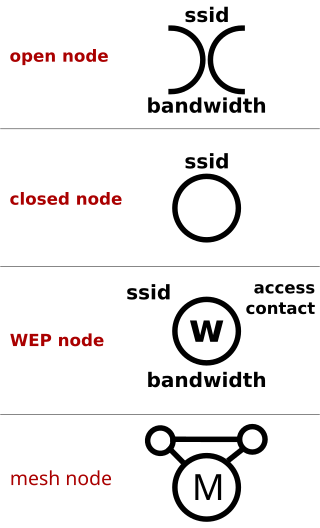
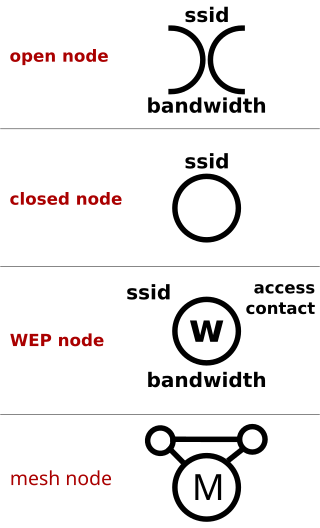
Warchalking is the drawing of symbols in public places to advertise an open Wi-Fi network. Inspired by hobo symbols, the warchalking marks were conceived by a group of friends in June 2002 and publicised by Matt Jones who designed the set of icons and produced a downloadable document containing them. Within days of Jones publishing a blog entry about warchalking, articles appeared in dozens of publications and stories appeared on several major television news programs around the world.

Wi-Fi is a family of wireless network protocols based on the IEEE 802.11 family of standards, which are commonly used for local area networking of devices and Internet access, allowing nearby digital devices to exchange data by radio waves. These are the most widely used computer networks, used globally in home and small office networks to link devices and to provide Internet access with wireless routers and wireless access points in public places such as coffee shops, hotels, libraries, and airports to provide visitors.
Wardialing is a technique to automatically scan a list of telephone numbers, usually dialing every number in a local area code to search for modems, computers, bulletin board systems and fax machines. Hackers use the resulting lists for various purposes: hobbyists for exploration, and crackers—malicious hackers who specialize in breaching computer security—for guessing user accounts, or locating modems that might provide an entry-point into computer or other electronic systems. It may also be used by security personnel, for example, to detect unauthorized devices, such as modems or faxes, on a company's telephone network.

A hotspot is a physical location where people can obtain Internet access, typically using Wi-Fi technology, via a wireless local-area network (WLAN) using a router connected to an Internet service provider.
Sony's LocationFree is the marketing name for a group of products and technologies for timeshifting and placeshifting streaming video. The LocationFree Player is an Internet-based multifunctional device used to stream live television broadcasts, DVDs and DVR content over a home network or the Internet. It is in essence a remote video streaming server product. It was first announced by Sony in Q1 2004 and launched early in Q4 2004 alongside a co-branded wireless tablet TV. The last LocationFree product was the LF-V30 released in 2007.

Tethering or phone-as-modem (PAM) is the sharing of a mobile device's Internet connection with other connected computers. Connection of a mobile device with other devices can be done over wireless LAN (Wi-Fi), over Bluetooth or by physical connection using a cable, for example through USB.
Wi-Fi calling refers to mobile phone voice calls and data that are made over IP networks using Wi-Fi, instead of the cell towers provided by cellular networks. Using this feature, compatible handsets are able to route regular cellular calls through a wireless LAN (Wi-Fi) network with broadband Internet, while seamlessly change connections between the two where necessary. This feature makes use of the Generic Access Network (GAN) protocol, also known as Unlicensed Mobile Access (UMA).
Piggybacking on Internet access is the practice of establishing a wireless Internet connection by using another subscriber's wireless Internet access service without the subscriber's explicit permission or knowledge. It is a legally and ethically controversial practice, with laws that vary by jurisdiction around the world. While completely outlawed or regulated in some places, it is permitted in others.
Skyhook is a location technology company based in Boston, Massachusetts, specializing in location positioning, context, and intelligence. Founded in 2003, Skyhook originally began by geolocating Wi-Fi access points. Since then, Skyhook has been focusing on hybrid positioning technology, incorporating with Wi-Fi, GPS, cell towers, IP address, and device sensors to improve device location.
Real-time geotagging refers to the automatic technique of acquiring media, associating a specific location with the media, transferring the media to an online map and publishing the media in real time. It is thus an extension of an automatic geotagging process, requiring an in-built or attached location acquisition device, but also requires communication with a wireless data transfer device. Most modern smartphones and several digital cameras already integrate camera, aGPS, and wireless data transfer into one device, thus directly producing a geotagged photograph. Real-time geotagging is sometimes referred to as "mobile geotagging" or "autogeotagging", but this does not imply the real-time publishing step.
Wi-Fi Direct is a Wi-Fi standard for peer-to-peer wireless connections that allows two devices to establish a direct Wi-Fi connection without an intermediary wireless access point, router, or Internet connection. Wi-Fi Direct is single-hop communication, rather than multi-hop communication like wireless ad hoc networks.
WiFi-Where was a tool that facilitated Wardriving and detection of wireless LANs using the 802.11b, 802.11a and 802.11g WLAN standards. Versions existed for the operating systems iOS and Palm OS. Originally created in June 2004 for the Palm OS by Jonathan Hays of Hazelware Software, the IP for WiFi-Where was licensed to 3Jacks Software in 2009. An iPhone version of the application was released in January 2010, but was pulled from the App Store by Apple in March 2010. The app was frequently listed as a common tool to facilitate Wardriving As of 2010, it is still available in the Jailbroken Cydia store.
A GSM Cell ID (CID) is a generally unique number used to identify each base transceiver station (BTS) or sector of a BTS within a location area code (LAC) if not within a GSM network.

WiGLE is a website for collecting information about the different wireless hotspots around the world. Users can register on the website and upload hotspot data like GPS coordinates, SSID, MAC address and the encryption type used on the hotspots discovered. In addition, cell tower data is uploaded and displayed.
Mobile security, or mobile device security, is the protection of smartphones, tablets, and laptops from threats associated with wireless computing. It has become increasingly important in mobile computing. The security of personal and business information now stored on smartphones is of particular concern.
Republic Wireless was an American mobile virtual network operator (MVNO). Republic sold low cost mobile phone service on partner networks. Republic started as a unique company that provided customers with VOIP numbers which relied on WiFi first with cell as a backup.
Smartphone ad hoc networks are wireless ad hoc networks that use smartphones. Once embedded with ad hoc networking technology, a group of smartphones in close proximity can together create an ad hoc network. Smart phone ad hoc networks use the existing hardware in commercially available smartphones to create peer-to-peer networks without relying on cellular carrier networks, wireless access points, or traditional network infrastructure. Wi-Fi SPANs use the mechanism behind Wi-Fi ad-hoc mode, which allows phones to talk directly among each other, through a transparent neighbor and route discovery mechanism. SPANs differ from traditional hub and spoke networks, such as Wi-Fi Direct, in that they support multi-hop routing and relays and there is no notion of a group leader, so peers can join and leave at will without destroying the network.
Mozilla Location Service (MLS) is an open geolocation service which allows devices to find their position by processing their received signals of publicly observable radio transmitters: cellular network antennae, Wi-Fi access points, and Bluetooth beacons. The service is provided by Mozilla since 2013. The service uses Mozilla's open source software project called Ichnaea.
Google Fi Wireless, formerly Project Fi and Google Fi, is an American MVNO telecommunications service by Google that provides telephone calls, SMS, and mobile broadband using cellular networks and Wi-Fi. Google Fi uses the T-Mobile network. Google Fi is a service for US residents only, as of late 2023.