Related Research Articles
Electronic mail is a method of transmitting and receiving messages using electronic devices. It was conceived in the late–20th century as the digital version of, or counterpart to, mail. Email is a ubiquitous and very widely used communication medium; in current use, an email address is often treated as a basic and necessary part of many processes in business, commerce, government, education, entertainment, and other spheres of daily life in most countries.

A password, sometimes called a passcode, is secret data, typically a string of characters, usually used to confirm a user's identity. Traditionally, passwords were expected to be memorized, but the large number of password-protected services that a typical individual accesses can make memorization of unique passwords for each service impractical. Using the terminology of the NIST Digital Identity Guidelines, the secret is held by a party called the claimant while the party verifying the identity of the claimant is called the verifier. When the claimant successfully demonstrates knowledge of the password to the verifier through an established authentication protocol, the verifier is able to infer the claimant's identity.

Phishing is a form of social engineering and a scam where attackers deceive people into revealing sensitive information or installing malware such as viruses, worms, adware, or ransomware. Phishing attacks have become increasingly sophisticated and often transparently mirror the site being targeted, allowing the attacker to observe everything while the victim navigates the site, and transverses any additional security boundaries with the victim. As of 2020, it is the most common type of cybercrime, with the FBI's Internet Crime Complaint Center reporting more incidents of phishing than any other type of computer crime.

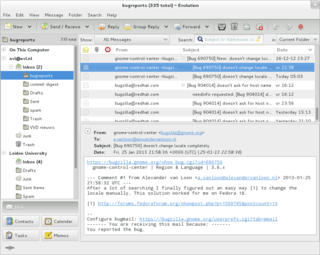
Gmail is the email service provided by Google. As of 2019, it had 1.5 billion active users worldwide, making it the largest email service in the world. It also provides a webmail interface, accessible through a web browser, and is also accessible through the official mobile application. Google also supports the use of third-party email clients via the POP and IMAP protocols.
Internet security is a branch of computer security. It encompasses the Internet, browser security, web site security, and network security as it applies to other applications or operating systems as a whole. Its objective is to establish rules and measures to use against attacks over the Internet. The Internet is an inherently insecure channel for information exchange, with high risk of intrusion or fraud, such as phishing, online viruses, trojans, ransomware and worms.
Single sign-on (SSO) is an authentication scheme that allows a user to log in with a single ID to any of several related, yet independent, software systems.
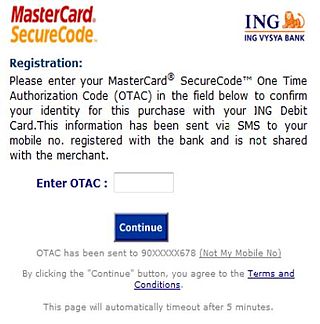
A one-time password (OTP), also known as a one-time PIN, one-time authorization code (OTAC) or dynamic password, is a password that is valid for only one login session or transaction, on a computer system or other digital device. OTPs avoid several shortcomings that are associated with traditional (static) password-based authentication; a number of implementations also incorporate two-factor authentication by ensuring that the one-time password requires access to something a person has as well as something a person knows.
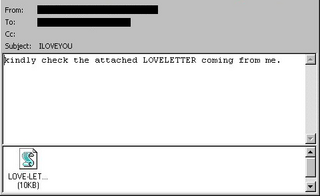
ILOVEYOU, sometimes referred to as the Love Bug or Loveletter, was a computer worm that infected over ten million Windows personal computers on and after 5 May 2000. It started spreading as an email message with the subject line "ILOVEYOU" and the attachment "LOVE-LETTER-FOR-YOU.TXT.vbs". At the time, Windows computers often hid the latter file extension by default because it is an extension for a file type that Windows knows, leading unwitting users to think it was a normal text file. Opening the attachment activates the Visual Basic script. First, the worm inflicts damage on the local machine, overwriting random files, then, it copies itself to all addresses in the Windows Address Book used by Microsoft Outlook, allowing it to spread much faster than any other previous email worm.

Outlook.com, formerly Hotmail, is a free personal email service offered by Microsoft. This includes a webmail interface featuring mail, calendaring, contacts, and tasks services. Outlook can also be accessed via email clients using the IMAP or POP protocols.

Multi-factor authentication is an electronic authentication method in which a user is granted access to a website or application only after successfully presenting two or more pieces of evidence to an authentication mechanism. MFA protects personal data—which may include personal identification or financial assets—from being accessed by an unauthorized third party that may have been able to discover, for example, a single password.
Trapster was a navigation social networking mobile application and website, provided for free, that maps out and alerts users in real time to the presence of live police speed traps, DUI checkpoints, traffic, red light cameras, speed cameras, and areas where police often hide. Further, it allows users to record trip data and share it via the web, including interfaces with Facebook and Twitter. Trapster was recognized by Time Magazine as one of the 10 Best iPhone Apps for Dads in June 2009. In addition, Wired listed Trapster as the number 1 application in their 10 Mobile Applications that Make the Most of Location and CNET named Trapster as their number 1 free iPhone automotive app.
A recent extension to the cultural relationship with death is the increasing number of people who die having created a large amount of digital content, such as social media profiles, that will remain after death. This may result in concern and confusion, because of automated features of dormant accounts, uncertainty of the deceased's preferences that profiles be deleted or left as a memorial, and whether information that may violate the deceased's privacy should be made accessible to family.
Apple Account, formerly known as Apple ID, is a user account by Apple for their devices and software. Apple Accounts contain the user's personal data and settings, and when an Apple Account is used to log in to an Apple device, the device will automatically use the data and settings associated with the Apple Account.

The Sarah Palin email hack occurred on September 16, 2008, during the 2008 United States presidential election campaign when vice presidential candidate Sarah Palin's personal Yahoo! email account was subjected to unauthorized access. The hacker, David Kernell, obtained access to Palin's account by looking up biographical details, such as her high school and birthdate, and using Yahoo!'s account recovery for forgotten passwords. Kernell then posted several pages of Palin's email on 4chan's /b/ board. Kernell, who at the time of the offense was a 20-year-old college student, was the son of longtime Democratic state representative Mike Kernell of Memphis.

Proton Mail is a Swiss end-to-end encrypted email service founded in 2013 headquartered in Plan-les-Ouates, Switzerland. It uses client-side encryption to protect email content and user data before they are sent to Proton Mail servers, unlike other common email providers such as Gmail and Outlook.com. The service can be accessed through a webmail client, the Tor network, Windows, macOS and Linux (beta) desktop apps and iOS and Android apps.

Have I Been Pwned? is a website that allows Internet users to check whether their personal data has been compromised by data breaches. The service collects and analyzes hundreds of database dumps and pastes containing information about billions of leaked accounts, and allows users to search for their own information by entering their username or email address. Users can also sign up to be notified if their email address appears in future dumps. The site has been widely touted as a valuable resource for Internet users wishing to protect their own security and privacy. Have I Been Pwned? was created by security expert Troy Hunt on 4 December 2013.
Credential stuffing is a type of cyberattack in which the attacker collects stolen account credentials, typically consisting of lists of usernames or email addresses and the corresponding passwords, and then uses the credentials to gain unauthorized access to user accounts on other systems through large-scale automated login requests directed against a web application. Unlike credential cracking, credential stuffing attacks do not attempt to use brute force or guess any passwords – the attacker simply automates the logins for a large number of previously discovered credential pairs using standard web automation tools such as Selenium, cURL, PhantomJS or tools designed specifically for these types of attacks, such as Sentry MBA, SNIPR, STORM, Blackbullet and Openbullet.
Internet security awareness or Cyber security awareness refers to how much end-users know about the cyber security threats their networks face, the risks they introduce and mitigating security best practices to guide their behavior. End users are considered the weakest link and the primary vulnerability within a network. Since end-users are a major vulnerability, technical means to improve security are not enough. Organizations could also seek to reduce the risk of the human element. This could be accomplished by providing security best practice guidance for end users' awareness of cyber security. Employees could be taught about common threats and how to avoid or mitigate them.
Passwordless authentication is an authentication method in which a user can log in to a computer system without the entering a password or any other knowledge-based secret. In most common implementations users are asked to enter their public identifier and then complete the authentication process by providing a secure proof of identity through a registered device or token.
References
- ↑ Cohen, David (17 January 2007). "Dimensions of the Deathswitch". The Guardian. ISSN 0261-3077 – via www.theguardian.com.
- ↑ Mooallem, Jon (20 November 2014). "The Startup That Lets You Communicate From Beyond the Grave". Wired. ISSN 1059-1028 . Retrieved 2019-10-04– via www.wired.com.
- ↑ AP, Kathy Willens / (15 March 2009). "In case of death, please send e-mail". msnbc.com. Retrieved 2019-10-04.
- ↑ Walker, Rob (5 January 2011). "Cyberspace When You're Dead". The New York Times . ISSN 0362-4331 . Retrieved 2019-10-04– via NYTimes.com.