Related Research Articles
Adware, often called advertising-supported software by its developers, is software that generates revenue for its developer by automatically generating online advertisements in the user interface of the software or on a screen presented to the user during the installation process. The software may generate two types of revenue: one is for the display of the advertisement and another on a "pay-per-click" basis, if the user clicks on the advertisement. Some advertisements also act as spyware, collecting and reporting data about the user, to be sold or used for targeted advertising or user profiling. The software may implement advertisements in a variety of ways, including a static box display, a banner display, a full screen, a video, a pop-up ad or in some other form. All forms of advertising carry health, ethical, privacy and security risks for users.
Malware is any software intentionally designed to cause disruption to a computer, server, client, or computer network, leak private information, gain unauthorized access to information or systems, deprive access to information, or which unknowingly interferes with the user's computer security and privacy. Researchers tend to classify malware into one or more sub-types.
Spyware is any software with malicious behavior that aims to gather information about a person or organization and send it to another entity in a way that harms the user by violating their privacy, endangering their device's security, or other means. This behavior may be present in malware and in legitimate software. Websites may engage in spyware behaviors like web tracking. Hardware devices may also be affected.
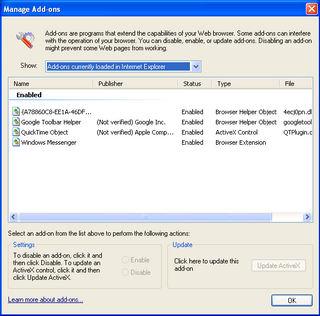
A Browser Helper Object (BHO) is a DLL module designed as a plugin for the Microsoft Internet Explorer web browser to provide added functionality. BHOs were introduced in October 1997 with the release of version 4 of Internet Explorer. Most BHOs are loaded once by each new instance of Internet Explorer. However, in the case of Windows Explorer, a new instance is launched for each window.
Norton AntiVirus is an anti-virus or anti-malware software product founded by Peter Norton, developed and distributed by Symantec since 1990 as part of its Norton family of computer security products. It uses signatures and heuristics to identify viruses. Other features included in it are e-mail spam filtering and phishing protection.
PDFCreator is an application for converting documents into Portable Document Format (PDF) format on Microsoft Windows operating systems. It works by creating a virtual printer that prints to PDF files, and thereby allows practically any application to create PDF files by choosing to print from within the application and then printing to the PDFCreator printer.
Crimeware is a class of malware designed specifically to automate cybercrime.
Browser hijacking is a form of unwanted software that modifies a web browser's settings without a user's permission, to inject unwanted advertising into the user's browser. A browser hijacker may replace the existing home page, error page, or search engine with its own. These are generally used to force hits to a particular website, increasing its advertising revenue.

WinFixer was a family of scareware rogue security programs developed by Winsoftware which claimed to repair computer system problems on Microsoft Windows computers if a user purchased the full version of the software. The software was mainly installed without the user's consent. McAfee claimed that "the primary function of the free version appears to be to alarm the user into paying for registration, at least partially based on false or erroneous detections." The program prompted the user to purchase a paid copy of the program.

Zango,, formerly ePIPO, 180solutions and Hotbar, was a software company that provided users access to its partners' videos, games, tools and utilities in exchange for viewing targeted advertising placed on their computers. Zango software is listed as adware by Symantec, and is also labeled as a potentially unwanted program by McAfee. Zango was co-founded by two brothers: Keith Smith, who served as the CEO; and Ken Smith, who served as the CTO.
Google Pack was a collection of software tools offered by Google to download in a single archive. It was announced at the 2006 Consumer Electronics Show, on January 6. Google Pack was only available for Windows XP, Windows Vista, and Windows 7.
Christopher Boyd, also known by his online pseudonym Paperghost, is a computer security researcher.
The Vundo Trojan is either a Trojan horse or a computer worm that is known to cause popups and advertising for rogue antispyware programs, and sporadically other misbehavior including performance degradation and denial of service with some websites including Google and Facebook. It also is used to deliver other malware to its host computers. Later versions include rootkits and ransomware.
Rogue security software is a form of malicious software and internet fraud that misleads users into believing there is a virus on their computer and aims to convince them to pay for a fake malware removal tool that actually installs malware on their computer. It is a form of scareware that manipulates users through fear, and a form of ransomware. Rogue security software has been a serious security threat in desktop computing since 2008. An early example that gained infamy was SpySheriff and its clones, such as Nava Shield.

SpySheriff is malware that disguises itself as anti-spyware software. It attempts to mislead the user with false security alerts, threatening them into buying the program. Like other rogue antiviruses, after producing a list of false threats, it prompts the user to pay to remove them. The software is particularly difficult to remove, since it nests its components in System Restore folders, and also blocks some system management tools. However, SpySheriff can be removed by an experienced user, antivirus software, or by using a rescue disk.
MS Antivirus is a scareware rogue anti-virus which purports to remove virus infections found on a computer running Microsoft Windows. It attempts to scam the user into purchasing a "full version" of the software. The company and the individuals behind Bakasoftware operated under other different 'company' names, including Innovagest2000, Innovative Marketing Ukraine, Pandora Software, LocusSoftware, etc.
Browser security is the application of Internet security to web browsers in order to protect networked data and computer systems from breaches of privacy or malware. Security exploits of browsers often use JavaScript, sometimes with cross-site scripting (XSS) with a secondary payload using Adobe Flash. Security exploits can also take advantage of vulnerabilities that are commonly exploited in all browsers.
Download Valley is a cluster of software companies in Israel, producing and delivering adware to be installed alongside downloads of other software. The primary purpose is to monetize shareware and downloads. These software items are commonly browser toolbars, adware, browser hijackers, spyware, and malware. Another group of products are download managers, possibly designed to induce or trick the user to install adware, when downloading a piece of desired software or mobile app from a certain source.
A potentially unwanted program (PUP) or potentially unwanted application (PUA) is software that a user may perceive as unwanted or unnecessary. It is used as a subjective tagging criterion by security and parental control products. Such software may use an implementation that can compromise privacy or weaken the computer's security. Companies often bundle a wanted program download with a wrapper application and may offer to install an unwanted application, and in some cases without providing a clear opt-out method. Antivirus companies define the software bundled as potentially unwanted programs which can include software that displays intrusive advertising (adware), or tracks the user's Internet usage to sell information to advertisers (spyware), injects its own advertising into web pages that a user looks at, or uses premium SMS services to rack up charges for the user. A growing number of open-source software projects have expressed dismay at third-party websites wrapping their downloads with unwanted bundles, without the project's knowledge or consent. Nearly every third-party free download site bundles their downloads with potentially unwanted software. The practice is widely considered unethical because it violates the security interests of users without their informed consent. Some unwanted software bundles install a root certificate on a user's device, which allows hackers to intercept private data such as banking details, without a browser giving security warnings. The United States Department of Homeland Security has advised removing an insecure root certificate, because they make computers vulnerable to serious cyberattacks. Software developers and security experts recommend that people always download the latest version from the official project website, or a trusted package manager or app store.
References
- 1 2 "Dyfuca". Panda Security.
- 1 2 "MoneyTree". Pest Patrol. Archived from the original on October 26, 2003. Retrieved October 12, 2018.
- ↑ "DyFuCa". F-Secure.