Related Research Articles

Bletchley Park is an English country house and estate in Milton Keynes (Buckinghamshire) that became the principal centre of Allied code-breaking during the Second World War. The mansion was constructed during the years following 1883 for the financier and politician Sir Herbert Leon in the Victorian Gothic, Tudor, and Dutch Baroque styles, on the site of older buildings of the same name.

Cryptanalysis is the study of analyzing information systems in order to study the hidden aspects of the systems. Cryptanalysis is used to breach cryptographic security systems and gain access to the contents of encrypted messages, even if the cryptographic key is unknown.

Colossus was a set of computers developed by British codebreakers in the years 1943–1945 to help in the cryptanalysis of the Lorenz cipher. Colossus used thermionic valves to perform Boolean and counting operations. Colossus is thus regarded as the world's first programmable, electronic, digital computer, although it was programmed by switches and plugs and not by a stored program.
A chosen-plaintext attack (CPA) is an attack model for cryptanalysis which presumes that the attacker can obtain the ciphertexts for arbitrary plaintexts. The goal of the attack is to gain information that reduces the security of the encryption scheme.

Fish was the UK's GC&CS Bletchley Park codename for any of several German teleprinter stream ciphers used during World War II. Enciphered teleprinter traffic was used between German High Command and Army Group commanders in the field, so its intelligence value (Ultra) was of the highest strategic value to the Allies. This traffic normally passed over landlines, but as German forces extended their geographic reach beyond western Europe, they had to resort to wireless transmission.
The known-plaintext attack (KPA) is an attack model for cryptanalysis where the attacker has access to both the plaintext, and its encrypted version (ciphertext). These can be used to reveal further secret information such as secret keys and code books. The term "crib" originated at Bletchley Park, the British World War II decryption operation, where it was defined as:
A plain language passage of any length, usually obtained by solving one or more cipher or code messages, and occurring or believed likely to occur in a different cipher or code message, which it may provide a means of solving.
In cryptography, a ciphertext-only attack (COA) or known ciphertext attack is an attack model for cryptanalysis where the attacker is assumed to have access only to a set of ciphertexts. While the attacker has no channel providing access to the plaintext prior to encryption, in all practical ciphertext-only attacks, the attacker still has some knowledge of the plaintext. For instance, the attacker might know the language in which the plaintext is written or the expected statistical distribution of characters in the plaintext. Standard protocol data and messages are commonly part of the plaintext in many deployed systems and can usually be guessed or known efficiently as part of a ciphertext-only attack on these systems.
In cryptanalysis, gardening is the act of encouraging a target to use known plaintext in an encrypted message. It was a term used at the British Government Code and Cypher School at Bletchley Park, England, during World War II, for schemes to entice the Germans to include particular words, which the British called "cribs", in their encrypted messages. This term presumably came from RAF minelaying missions, or "gardening" sorties. "Gardening" was standard RAF slang for sowing mines in rivers, ports and oceans from low heights, possibly because each sea area around the European coasts was given a code-name of flowers or vegetables.

The bombe is an electro-mechanical device used by the British cryptologists to help decipher German Enigma-machine-encrypted secret messages during World War II. The US Navy and US Army later produced their own machines to the same functional specification, albeit engineered differently both from each other and from Polish and British bombes.
Cryptanalysis of the Enigma ciphering system enabled the western Allies in World War II to read substantial amounts of Morse-coded radio communications of the Axis powers that had been enciphered using Enigma machines. This yielded military intelligence which, along with that from other decrypted Axis radio and teleprinter transmissions, was given the codename Ultra. This was considered by western Supreme Allied Commander Dwight D. Eisenhower to have been "decisive" to Allied victory.
Cryptography was used extensively during World War II, with a plethora of code and cipher systems fielded by the nations involved. In addition, the theoretical and practical aspects of cryptanalysis, or codebreaking, were much advanced.

The method of Zygalski sheets was a cryptologic technique used by the Polish Cipher Bureau before and during World War II, and during the war also by British cryptologists at Bletchley Park, to decrypt messages enciphered on German Enigma machines.
Alfred Dillwyn "Dilly" Knox, CMG was a British classics scholar and papyrologist at King's College, Cambridge and a codebreaker. As a member of the Room 40 codebreaking unit he helped decrypt the Zimmermann Telegram which brought the USA into the First World War. He then joined the Government Code and Cypher School (GC&CS).
Harold Hall "Doc" Keen (1894–1973) was a British engineer who produced the engineering design, and oversaw the construction of, the British bombe, a codebreaking machine used in World War II to read German messages sent using the Enigma machine. He was known as "Doc" Keen because of his habit of carrying tools and paperwork in a case resembling a doctor's bag. After the war he was awarded the O.B.E..
In cryptanalysis, attack models or attack types are a classification of cryptographic attacks specifying the kind of access a cryptanalyst has to a system under attack when attempting to "break" an encrypted message generated by the system. The greater the access the cryptanalyst has to the system, the more useful information he can get to utilize for breaking the cypher.
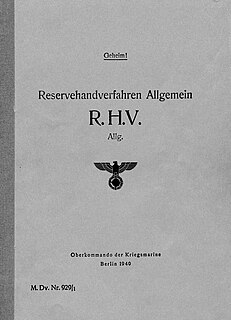
Reservehandverfahren (RHV) was a German Naval World War II hand-cipher system used as a backup method when no working Enigma machine was available.

Rolf Noskwith was a British businessman who during the Second World War worked under Alan Turing as a cryptographer at the Bletchley Park British military base.
Cryptanalysis of the Lorenz cipher was the process that enabled the British to read high-level German army messages during World War II. The British Government Code and Cypher School (GC&CS) at Bletchley Park decrypted many communications between the Oberkommando der Wehrmacht in Berlin and their army commands throughout occupied Europe, some of which were signed "Adolf Hitler, Führer". These were intercepted non-Morse radio transmissions that had been enciphered by the Lorenz SZ teleprinter rotor stream cipher attachments. Decrypts of this traffic became an important source of "Ultra" intelligence, which contributed significantly to Allied victory.
The Short Weather Cipher, also known as the weather short signal book, was a cipher, presented as a codebook, that was used by the radio telegraphists aboard U-boats of the German Navy (Kriegsmarine) during World War II. It was used to condense weather reports into a short 7-letter message, which was enciphered by using the naval Enigma and transmitted by radiomen to intercept stations on shore, where it was deciphered by Enigma and the 7-letter weather report was reconstructed.
Wahlwort is a cryptographic term used particularly in connection with the Wehrmacht, which used wahlworts on their Enigma rotor machine in the encryption of their communication in World War II. The term describes a randomly selected word which was inserted at the beginning or end of the radiogram plaintext. The wahlwort was intended to hinder the enemy’s cryptanalysis and prevent the decryption of the ciphertext.
References
- ↑ Smith & Erskine (2001) p 69
- Smith, Michael and Erskine, Ralph (editors): Action this Day (2001, Bantam London) ISBN 0-593-04910-1