Related Research Articles

A password, sometimes called a passcode, is secret data, typically a string of characters, usually used to confirm a user's identity. Traditionally, passwords were expected to be memorized, but the large number of password-protected services that a typical individual accesses can make memorization of unique passwords for each service impractical. Using the terminology of the NIST Digital Identity Guidelines, the secret is held by a party called the claimant while the party verifying the identity of the claimant is called the verifier. When the claimant successfully demonstrates knowledge of the password to the verifier through an established authentication protocol, the verifier is able to infer the claimant's identity.

An email client, email reader or, more formally, message user agent (MUA) or mail user agent is a computer program used to access and manage a user's email.

Phishing is a form of social engineering and scam where attackers deceive people into revealing sensitive information or installing malware such as ransomware. Phishing attacks have become increasingly sophisticated and often transparently mirror the site being targeted, allowing the attacker to observe everything while the victim is navigating the site, and transverse any additional security boundaries with the victim. As of 2020, it is the most common type of cybercrime, with the FBI's Internet Crime Complaint Center reporting more incidents of phishing than any other type of computer crime.

Internet security is a branch of computer security. It encompasses the Internet, browser security, web site security, and network security as it applies to other applications or operating systems as a whole. Its objective is to establish rules and measures to use against attacks over the Internet. The Internet is an inherently insecure channel for information exchange, with high risk of intrusion or fraud, such as phishing, online viruses, trojans, ransomware and worms.
Single sign-on (SSO) is an authentication scheme that allows a user to log in with a single ID to any of several related, yet independent, software systems.
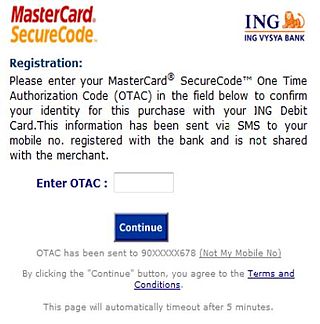
A one-time password (OTP), also known as a one-time PIN, one-time authorization code (OTAC) or dynamic password, is a password that is valid for only one login session or transaction, on a computer system or other digital device. OTPs avoid several shortcomings that are associated with traditional (static) password-based authentication; a number of implementations also incorporate two-factor authentication by ensuring that the one-time password requires access to something a person has as well as something a person knows.
In computer science, session hijacking, sometimes also known as cookie hijacking, is the exploitation of a valid computer session—sometimes also called a session key—to gain unauthorized access to information or services in a computer system. In particular, it is used to refer to the theft of a magic cookie used to authenticate a user to a remote server. It has particular relevance to web developers, as the HTTP cookies used to maintain a session on many websites can be easily stolen by an attacker using an intermediary computer or with access to the saved cookies on the victim's computer. After successfully stealing appropriate session cookies an adversary might use the Pass the Cookie technique to perform session hijacking. Cookie hijacking is commonly used against client authentication on the internet. Modern web browsers use cookie protection mechanisms to protect the web from being attacked.
There are several forms of software used to help users or organizations better manage passwords:
Password fatigue is the feeling experienced by many people who are required to remember an excessive number of passwords as part of their daily routine, such as to log in to a computer at work, undo a bicycle lock or conduct banking from an automated teller machine. The concept is also known as password chaos, or more broadly as identity chaos.
Call avoidance is a strategy businesses use to reduce inbound call volumes to contact centers in the customer service industry, particularly in the consumer market.
A security question is form of shared secret used as an authenticator. It is commonly used by banks, cable companies and wireless providers as an extra security layer.

Multi-factor authentication is an electronic authentication method in which a user is granted access to a website or application only after successfully presenting two or more pieces of evidence to an authentication mechanism. MFA protects personal data—which may include personal identification or financial assets—from being accessed by an unauthorized third party that may have been able to discover, for example, a single password.
Apple ID is a user account by Apple for their devices and software. Apple IDs contain the user's personal data and settings. When an Apple ID is used to log in to an Apple device, the device will automatically use the data and settings associated with the Apple ID.
A Microsoft account or MSA is a single sign-on personal user account for Microsoft customers to log in to consumer Microsoft services, devices running on one of Microsoft's current operating systems, and Microsoft application software.
SQRL or Secure, Quick, Reliable Login is a draft open standard for secure website login and authentication. The software typically uses a link of the scheme sqrl:// or optionally a QR code, where a user identifies via a pseudonymous zero-knowledge proof rather than providing a user ID and password. This method is thought to be impervious to a brute-force password attack or data breach. It shifts the burden of security away from the party requesting the authentication and closer to the operating-system implementation of what is possible on the hardware, as well as to the user. SQRL was proposed by Steve Gibson of Gibson Research Corporation in October 2013 as a way to simplify the process of authentication without the risk of revelation of information about the transaction to a third party.
Identity-based security is a type of security that focuses on access to digital information or services based on the authenticated identity of an entity. It ensures that the users and services of these digital resources are entitled to what they receive. The most common form of identity-based security involves the login of an account with a username and password. However, recent technology has evolved into fingerprinting or facial recognition.

Proton Mail is a Swiss end-to-end encrypted email service founded in 2013 headquartered in Plan-les-Ouates, Switzerland. It uses client-side encryption to protect email content and user data before they are sent to Proton Mail servers, unlike other common email providers such as Gmail and Outlook.com. The service can be accessed through a webmail client, the Tor network, or dedicated iOS and Android apps.
Intuitive Password is a proprietary freemium password manager and secure digital wallet that stores users' passwords and confidential data. It was launched in 2013 by the Australian company Intuitive Security Systems. Intuitive Password received mixed reviews. Neil J. Rubeking wrote in PC Magazine in 2013 that Intuitive Password's not having automated password capture like some of its competitors was a significant downside.
In cybersecurity, cyber self-defense refers to self-defense against cyberattack. While it generally emphasizes active cybersecurity measures by computer users themselves, cyber self-defense is sometimes used to refer to the self-defense of organizations as a whole, such as corporate entities or entire nations. Surveillance self-defense is a variant of cyber self-defense and largely overlaps with it. Active and passive cybersecurity measures provide defenders with higher levels of cybersecurity, intrusion detection, incident handling and remediation capabilities. Various sectors and organizations are legally obligated to adhere to cyber security standards.

Bitwarden is a freemium open-source password management service that stores sensitive information such as website credentials in an encrypted vault. The platform offers a variety of client applications including a web interface, desktop applications, browser extensions, mobile apps, and a command-line interface. Bitwarden offers a free US or European cloud-hosted service as well as the ability to self-host.
References
- ↑ Griffith, Virgil (2005). "Messin' with Texas Deriving Mother's Maiden Names Using Public Records". Applied Cryptography and Network Security (PDF). Lecture Notes in Computer Science. Vol. 3531. pp. 91–103. doi:10.1007/11496137_7. ISBN 978-3-540-26223-7.
- ↑ Rabkin, Ariel (2008). "Personal knowledge questions for fallback authentication: Security questions in the era of Facebook" (PDF). Proceedings of the 4th symposium on Usable privacy and security. pp. 13–23. doi:10.1145/1408664.1408667. ISBN 9781605582764. S2CID 6309745.
- ↑ "Hacker impersonated Palin, stole e-mail password". 18 September 2008. Archived from the original on 2 October 2008.
- ↑ Jakobsson, Markus; et al. (2008). "Love and Authentication" (PDF). Proceeding of the twenty-sixth annual CHI conference on Human factors in computing systems - CHI '08. pp. 197–200. CiteSeerX 10.1.1.145.6934 . doi:10.1145/1357054.1357087. ISBN 9781605580111. S2CID 2199454. Archived from the original (PDF) on 2017-04-25. Retrieved 2021-04-30.
- ↑ Jakobsson, Markus; et al. (2008). "Quantifying the Security of preference-based Authentication" (PDF). Proceedings of the 4th ACM workshop on Digital identity management - DIM '08. pp. 61–70. CiteSeerX 10.1.1.150.7577 . doi:10.1145/1456424.1456435. ISBN 9781605582948. S2CID 16199928.
- ↑ Crawford, Duane; et al. (1986). "The Stability of Leisure Preferences". Journal of Leisure Research. 18 (2): 96–115. doi:10.1080/00222216.1986.11969649.
- ↑ Cox, Joseph (15 April 2016). "Enable This Setting So People Can't Guess Your Email Address from Your Twitter" . Retrieved 17 January 2021.
- ↑ Inference Solutions (2015). "Self-service password reset: Pipe dream or reality? - Inference". Archived from the original on 2016-03-05. Retrieved 2015-05-20.
- ↑ Finetti, Mario (30 January 2022). "Self service password reset in large organisations".
- ↑ RSA Laboratories (2006). "Fourth-factor authentication: Somebody you know" (PDF). Proceedings of the 13th ACM conference on Computer and communications security. pp. 168–178. doi:10.1145/1180405.1180427. ISBN 978-1595935182. S2CID 1979527.