A boot disk is a removable digital data storage medium from which a computer can load and run (boot) an operating system or utility program. The computer must have a built-in program which will load and execute a program from a boot disk meeting certain standards.

A COM file is a type of simple executable file. On the Digital Equipment Corporation (DEC) VAX operating systems of the 1970s, .COM was used as a filename extension for text files containing commands to be issued to the operating system. With the introduction of Digital Research's CP/M, the type of files commonly associated with COM extension changed to that of executable files. This convention was later carried over to DOS. Even when complemented by the more general EXE file format for executables, the compact COM files remained viable and frequently used under DOS.

A bootloader, also spelled as boot loader or called bootstrap loader, is a computer program that is responsible for booting a computer. If it also provides an interactive menu with multiple boot choices then it's often called a boot manager.
Abraxas, also known as Abraxas5, discovered in April 1993, is an encrypted, overwriting, file infecting computer virus which infects .COM and .EXE files, although it does not infect command.com. It does not become memory resident. Each time an infected file is executed, Abraxas infects the copy of dosshell.com located in the C:\DOS directory, as well as one EXE file in the current directory. Due to a bug in the virus, only the first EXE file in any directory is infected.
Acid is a computer virus which infects .COM and .EXE files including command.com. Each time an infected file is executed, Acid infects all of the .EXE files in the current directory. Later, if an infected file is executed, it infects the .COM files in the current directory. Programs infected with Acid will have had the first 792 bytes of the host program overwritten with Acid's own code. There will be no file length increase unless the original host program was smaller than 792 bytes, in which case it will become 792 bytes in length. The program's date and time in the DOS disk directory listing will not be altered.
Acme is a computer virus which infects MS-DOS EXE files. Each time an infected file is executed, Acme may infect an EXE in the current directory by creating a hidden 247 byte long read-only COM file with the same base name. Acme is a variant of Clonewar, a spawning virus. Acme is also perhaps a descendant of the small single-step infector Zeno, which is not to be confused with the Zeno programming language.
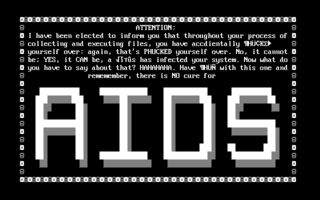
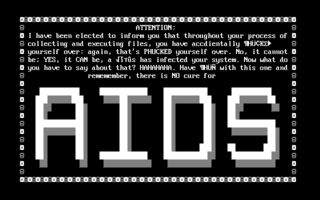
AIDS is a DOS computer virus which overwrites COM files.
The Michelangelo virus is a computer virus first discovered on 3 February 1991 in Australia. The virus was designed to infect DOS systems, but did not engage the operating system or make any OS calls. Michelangelo, like all boot sector viruses, operated at the BIOS level. Each year, the virus remained dormant until March 6, the birthday of Renaissance artist Michelangelo. There is no reference to the artist in the virus, and it is doubtful that the virus's developer(s) intended a connection between the virus and the artist. The name was chosen by researchers who noticed the coincidence of the activation date. The actual significance of the date to the author is unknown. Michelangelo is a variant of the already endemic Stoned virus.
ABC, discovered in October 1992, is a memory-resident, file-infecting computer virus which infects EXE files and may alter both COM and EXE files. ABC activates on the 13th day of every month.
Jerusalem is a logic bomb DOS virus first detected at Hebrew University of Jerusalem, in October 1987. On infection, the Jerusalem virus becomes memory resident, and then infects every executable file run, except for COMMAND.COM. COM files grow by 1,813 bytes when infected by Jerusalem and are not re-infected. Executable files grow by 1,808 to 1,823 bytes each time they are infected, and are then re-infected each time the files are loaded until they are too large to load into memory. Some .EXE files are infected but do not grow because several overlays follow the genuine .EXE file in the same file. Sometimes .EXE files are incorrectly infected, causing the program to fail to run as soon as it is executed.
Westwood is a computer virus, a variant of the Jerusalem family, discovered August 1990, in Westwood, Los Angeles, California. The virus was isolated by a UCLA engineering student who discovered it in a copy of the "speed.com" program distributed with a new motherboard. Viral infection was first indicated when an early version of Microsoft Word reported internal checksum failure and failed to run.
Scott's Valley [sic] is a computer virus, a member of the Slow virus family and distantly related to the Jerusalem virus family. It was discovered in September 1990 in Scotts Valley, California.
Alabama is a computer virus, discovered in October 1989 on the campus of the Hebrew University of Jerusalem.
Ontario is a family of computer viruses, named after its point of isolation, the Canadian province of Ontario. This family of computer virus consists of Ontario.1024, Ontario.512 and Ontario.2048. The first variant Ontario.512 was discovered in July 1990. Because Ontario.1024 was also discovered in Ontario, it is likely that both viruses originate from within the province. By the Ontario.2048 variant, the author had adopted "Ontario" as the family's name and even included the name "Ontario-3" in the virus code.
Form was a boot sector virus isolated in Switzerland in the summer of 1990 which became very common worldwide. The origin of Form is widely listed as Switzerland, but this may be an assumption based on its isolation locale. The only notable characteristics of Form are that it infects the boot sector instead of the Master Boot Record (MBR) and the clicking noises associated with some infections. Infections under Form can result in severe data damage if operating system characteristics are not identical to those Form assumes.
The Whale virus is a computer virus discovered on July 1, 1990. The file size, at 9,216 bytes, was for its time the largest virus ever discovered. It is known for using several advanced "stealth" methods.
KoKo Virus is a memory resident computer virus created in March 1991. KoKo's name came from the creator himself, which was a nickname used by his friends. Many on-line virus databases refer to KoKo as Koko.1780. KoKo is written in the Assembly programming language and the executable file usually has an approximate file size of around 1780 bytes.

A computer virus is a type of malware that, when executed, replicates itself by modifying other computer programs and inserting its own code into those programs. If this replication succeeds, the affected areas are then said to be "infected" with a computer virus, a metaphor derived from biological viruses.
ANTI is a computer virus affecting Apple Macintosh computers running classic Mac OS versions up to System 6. It was the first Macintosh virus not to create additional resources within infected files; instead, it patches existing CODE resources.