The Defense Advanced Research Projects Agency (DARPA) is a research and development agency of the United States Department of Defense responsible for the development of emerging technologies for use by the military. Originally known as the Advanced Research Projects Agency (ARPA), the agency was created on February 7, 1958, by President Dwight D. Eisenhower in response to the Soviet launching of Sputnik 1 in 1957. By collaborating with academia, industry, and government partners, DARPA formulates and executes research and development projects to expand the frontiers of technology and science, often beyond immediate U.S. military requirements. The name of the organization first changed from its founding name, ARPA, to DARPA, in March 1972, changing back to ARPA in February 1993, then reverted to DARPA in March 1996.

In computer networking, a thin client, sometimes called slim client or lean client, is a simple (low-performance) computer that has been optimized for establishing a remote connection with a server-based computing environment. They are sometimes known as network computers, or in their simplest form as zero clients. The server does most of the work, which can include launching software programs, performing calculations, and storing data. This contrasts with a rich client or a conventional personal computer; the former is also intended for working in a client–server model but has significant local processing power, while the latter aims to perform its function mostly locally.

An embedded system is a specialized computer system—a combination of a computer processor, computer memory, and input/output peripheral devices—that has a dedicated function within a larger mechanical or electronic system. It is embedded as part of a complete device often including electrical or electronic hardware and mechanical parts. Because an embedded system typically controls physical operations of the machine that it is embedded within, it often has real-time computing constraints. Embedded systems control many devices in common use. In 2009, it was estimated that ninety-eight percent of all microprocessors manufactured were used in embedded systems.
In computer networking, a rich client is a computer that typically provides rich functionality independent of the central server. This kind of computer was originally known as just a "client" or "thick client," in contrast with "thin client", which describes a computer heavily dependent on a server's applications. A rich client may be described as having a rich user interaction.
Linux Terminal Server Project (LTSP) is a free and open-source terminal server for Linux that allows many people to simultaneously use the same computer. Applications run on the server with a terminal known as a thin client handling input and output. Generally, terminals are low-powered, lack a hard disk and are quieter and more reliable than desktop computers because they do not have any moving parts.

A diskless node is a workstation or personal computer without disk drives, which employs network booting to load its operating system from a server.
The 140 series of Federal Information Processing Standards (FIPS) are U.S. government computer security standards that specify requirements for cryptographic modules.
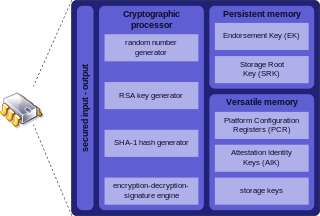
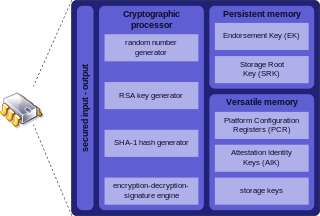
Trusted Platform Module (TPM) is an international standard for a secure cryptoprocessor, a dedicated microcontroller designed to secure hardware through integrated cryptographic keys. The term can also refer to a chip conforming to the standard ISO/IEC 11889. Common uses are to verify platform integrity, and to store disk encryption keys.
Information security standards are techniques generally outlined in published materials that attempt to protect a user's or organization's cyber environment. This environment includes users themselves, networks, devices, all software, processes, information in storage or transit, applications, services, and systems that can be connected directly or indirectly to networks.

MIL-STD-810, U.S. Department of Defense Test Method Standard, Environmental Engineering Considerations and Laboratory Tests, is a United States Military Standard that emphasizes tailoring an equipment's environmental design and test limits to the conditions that it will experience throughout its service life, and establishing chamber test methods that replicate the effects of environments on the equipment rather than imitating the environments themselves. Although prepared specifically for U.S. military applications, the standard is often applied for commercial products as well.
A rugged computer or ruggedized computer is a computer specifically designed to operate reliably in harsh usage environments and conditions, such as strong vibrations, extreme temperatures and wet or dusty conditions. They are designed from inception for the type of rough use typified by these conditions, not just in the external housing but in the internal components and cooling arrangements as well.
Electronic packaging is the design and production of enclosures for electronic devices ranging from individual semiconductor devices up to complete systems such as a mainframe computer. Packaging of an electronic system must consider protection from mechanical damage, cooling, radio frequency noise emission and electrostatic discharge. Product safety standards may dictate particular features of a consumer product, for example, external case temperature or grounding of exposed metal parts. Prototypes and industrial equipment made in small quantities may use standardized commercially available enclosures such as card cages or prefabricated boxes. Mass-market consumer devices may have highly specialized packaging to increase consumer appeal. Electronic packaging is a major discipline within the field of mechanical engineering.

Desktop virtualization is a software technology that separates the desktop environment and associated application software from the physical client device that is used to access it.
A web desktop or webtop is a desktop environment embedded in a web browser or similar client application. A webtop integrates web applications, web services, client–server applications, application servers, and applications on the local client into a desktop environment using the desktop metaphor. Web desktops provide an environment similar to that of Windows, Mac, or a graphical user interface on Unix and Linux systems. It is a virtual desktop running in a web browser. In a webtop the applications, data, files, configuration, settings, and access privileges reside remotely over the network. Much of the computing takes place remotely. The browser is primarily used for display and input purposes.
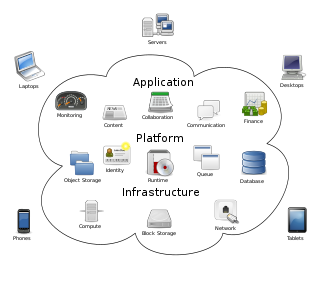
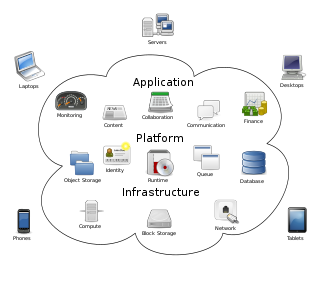
Cloud computing is the on-demand availability of computer system resources, especially data storage and computing power, without direct active management by the user. Large clouds often have functions distributed over multiple locations, each of which is a data center. Cloud computing relies on sharing of resources to achieve coherence and typically uses a pay-as-you-go model, which can help in reducing capital expenses but may also lead to unexpected operating expenses for users.
Reliability of a semiconductor device is the ability of the device to perform its intended function during the life of the device in the field.

Package testing or packaging testing involves the measurement of a characteristic or property involved with packaging. This includes packaging materials, packaging components, primary packages, shipping containers, and unit loads, as well as the associated processes.

Military Specification MIL-S-901D is for high-impact mechanical shock which applies to equipment mounted on ships. Its publication date was Mar 17, 1989. Two levels apply: Grade A items are items which are essential to the safety and continued combat capability of the ship; Grade B items are items whose operation is not essential to the safety and combat capability of the ship but which could become a hazard to personnel, to Grade A items, or to the ship as a whole as a result of exposure to shock. "Grade C", signifying that no shock qualification is required, is also sometimes referenced in acquisition documents even though the term has no official standing in the specification document. Qualification testing is performed on a specified machine or on a barge floating in a pond where an explosive charge is detonated at various distances and depths in the pond to impart shock to the barges.
Panasonic Toughpad is a series of tablet computers developed and designed by Panasonic as a subset of its series of Toughbook rugged computers. The first Toughpad was unveiled on November 7, 2011 in the United States.
TransApps was a program of the Defense Advanced Research Projects Agency (DARPA) of the United States Department of Defense. The goal of the program was to demonstrate rapid development and fielding of secure mobile apps on the battlefield. With its agile and user-centric approach, the DARPA program specifically addressed the limitations of the slow requirements-centric software development cycle followed by many Army programs of record.