A logic analyzer is an electronic instrument that captures and displays multiple logic signals from a digital system or digital circuit. A logic analyzer may convert the captured data into timing diagrams, protocol decodes, state machine traces, opcodes, or may correlate opcodes with source-level software. Logic analyzers have advanced triggering capabilities, and are useful when a user needs to see the timing relationships between many signals in a digital system.
Data communication or digital communications, including data transmission and data reception, is the transfer and reception of data in the form of a digital bitstream or a digitized analog signal transmitted over a point-to-point or point-to-multipoint communication channel. Examples of such channels are copper wires, optical fibers, wireless communication using radio spectrum, storage media and computer buses. The data are represented as an electromagnetic signal, such as an electrical voltage, radiowave, microwave, or infrared signal.
In telecommunications and computer networking, a network packet is a formatted unit of data carried by a packet-switched network. A packet consists of control information and user data; the latter is also known as the payload. Control information provides data for delivering the payload. Typically, control information is found in packet headers and trailers.

A packet analyzer, also known as packet sniffer, protocol analyzer, or network analyzer, is a computer program or computer hardware such as a packet capture appliance that can analyze and log traffic that passes over a computer network or part of a network. Packet capture is the process of intercepting and logging traffic. As data streams flow across the network, the analyzer captures each packet and, if needed, decodes the packet's raw data, showing the values of various fields in the packet, and analyzes its content according to the appropriate RFC or other specifications.
In telecommunications and computer networks, a channel access method or multiple access method allows more than two terminals connected to the same transmission medium to transmit over it and to share its capacity. Examples of shared physical media are wireless networks, bus networks, ring networks and point-to-point links operating in half-duplex mode.

A communication channel refers either to a physical transmission medium such as a wire, or to a logical connection over a multiplexed medium such as a radio channel in telecommunications and computer networking. A channel is used for information transfer of, for example, a digital bit stream, from one or several senders to one or several receivers. A channel has a certain capacity for transmitting information, often measured by its bandwidth in Hz or its data rate in bits per second.

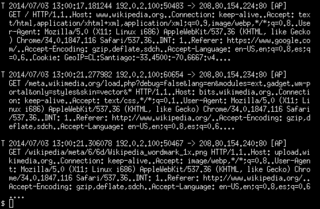
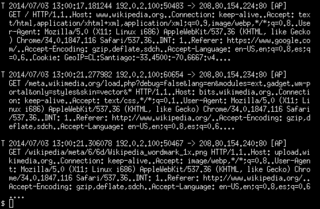
tcpdump is a data-network packet analyzer computer program that runs under a command line interface. It allows the user to display TCP/IP and other packets being transmitted or received over a network to which the computer is attached. Distributed under the BSD license, tcpdump is free software.
Deep packet inspection (DPI) is a type of data processing that inspects in detail the data being sent over a computer network, and may take actions such as alerting, blocking, re-routing, or logging it accordingly. Deep packet inspection is often used for baselining application behavior, analyzing network usage, troubleshooting network performance, ensuring that data is in the correct format, checking for malicious code, eavesdropping, and internet censorship, among other purposes. There are multiple headers for IP packets; network equipment only needs to use the first of these for normal operation, but use of the second header is normally considered to be shallow packet inspection despite this definition.
In the field of computer network administration, pcap is an application programming interface (API) for capturing network traffic. While the name is an abbreviation of packet capture, that is not the API's proper name. Unix-like systems implement pcap in the libpcap library; for Windows, there is a port of libpcap named WinPcap that is no longer supported or developed, and a port named Npcap for Windows 7 and later that is still supported.

A bus analyzer is a type of a protocol analysis tool, used for capturing and analyzing communication data across a specific interface bus, usually embedded in a hardware system. The bus analyzer functionality helps design, test and validation engineers to check, test, debug and validate their designs throughout the design cycles of a hardware-based product. It also helps in later phases of a product life cycle, in examining communication interoperability between systems and between components, and clarifying hardware support concerns.
Packet crafting is a technique that allows network administrators to probe firewall rule-sets and find entry points into a targeted system or network. This is done by manually generating packets to test network devices and behaviour, instead of using existing network traffic. Testing may target the firewall, IDS, TCP/IP stack, router or any other component of the network. Packets are usually created by using a packet generator or packet analyzer which allows for specific options and flags to be set on the created packets. The act of packet crafting can be broken into four stages: Packet Assembly, Packet Editing, Packet Play and Packet Decoding. Tools exist for each of the stages - some tools are focused only on one stage while others such as Ostinato try to encompass all stages.
An analyser or analyzer is a tool used to analyze data. For example, a gas analyzer tool is used to analyze gases. It examines the given data and tries to find patterns and relationships. An analyser can be a piece of hardware or software.

Wireshark is a free and open-source packet analyzer. It is used for network troubleshooting, analysis, software and communications protocol development, and education. Originally named Ethereal, the project was renamed Wireshark in May 2006 due to trademark issues.
ControlNet is an open industrial network protocol for industrial automation applications, also known as a fieldbus. ControlNet was earlier supported by ControlNet International, but in 2008 support and management of ControlNet was transferred to ODVA, which now manages all protocols in the Common Industrial Protocol family.

EtherApe is a packet sniffer/network traffic monitoring tool, developed for Unix. EtherApe is free, open source software developed under the GNU General Public License.
ngrep is a network packet analyzer written by Jordan Ritter. It has a command-line interface, and relies upon the pcap library and the GNU regex library.
Justniffer is a TCP packet sniffer. It can log network traffic in a 'standard' or in a customized way. It can also log response times, useful for tracking network services performances . The output format of the traffic can be easily customized. An example written in Python stores the transferred contents in an output directory separated by domains. This means that the transferred files like html, css, javascript, images, sounds, etc. can be saved to a directory.
CommView is an application for network monitoring, packet analysis, and decoding. There are two editions of CommView: the standard edition for Ethernet networks and the wireless edition for 802.11 networks named CommView for WiFi. The application runs on Microsoft Windows. It is developed by TamoSoft, a privately held New Zealand company founded in 1998.
Xplico is a network forensics analysis tool (NFAT), which is a software that reconstructs the contents of acquisitions performed with a packet sniffer.

The Sniffer was a computer network packet and protocol analyzer developed and first sold in 1986 by Network General Corporation of Mountain View, CA. By 1994 the Sniffer had become the market leader in high-end protocol analyzers. According to SEC 10-K filings and corporate annual reports, between 1986 and March 1997 about $933M worth of Sniffers and related products and services had been sold as tools for network managers and developers.