Related Research Articles
IEEE 802.1X is an IEEE Standard for port-based Network Access Control (PNAC). It is part of the IEEE 802.1 group of networking protocols. It provides an authentication mechanism to devices wishing to attach to a LAN or WLAN.

A captive portal is a web page accessed with a web browser that is displayed to newly connected users of a Wi-Fi or wired network before they are granted broader access to network resources. Captive portals are commonly used to present a landing or log-in page which may require authentication, payment, acceptance of an end-user license agreement, acceptable use policy, survey completion, or other valid credentials that both the host and user agree to adhere by. Captive portals are used for a broad range of mobile and pedestrian broadband services - including cable and commercially provided Wi-Fi and home hotspots. A captive portal can also be used to provide access to enterprise or residential wired networks, such as apartment houses, hotel rooms, and business centers.
IEEE 802.11i-2004, or 802.11i for short, is an amendment to the original IEEE 802.11, implemented as Wi-Fi Protected Access II (WPA2). The draft standard was ratified on 24 June 2004. This standard specifies security mechanisms for wireless networks, replacing the short Authentication and privacy clause of the original standard with a detailed Security clause. In the process, the amendment deprecated broken Wired Equivalent Privacy (WEP), while it was later incorporated into the published IEEE 802.11-2007 standard.
Java Authentication and Authorization Service, or JAAS, pronounced "Jazz", is the Java implementation of the standard Pluggable Authentication Module (PAM) information security framework. JAAS was introduced as an extension library to the Java Platform, Standard Edition 1.3 and was integrated in version 1.4.
NX technology, commonly known as NX, is a proprietary software application for remote access, desktop sharing, virtual desktop and file transfer between computers. It is developed by the Luxembourg-based company NoMachine which also lends its name to the software.
Extensible Authentication Protocol (EAP) is an authentication framework frequently used in network and internet connections. It is defined in RFC 3748, which made RFC 2284 obsolete, and is updated by RFC 5247. EAP is an authentication framework for providing the transport and usage of material and parameters generated by EAP methods. There are many methods defined by RFCs and a number of vendor specific methods and new proposals exist. EAP is not a wire protocol; instead it only defines the information from the interface and the formats. Each protocol that uses EAP defines a way to encapsulate by the user EAP messages within that protocol's messages.
Xsupplicant is a supplicant that allows a workstation to authenticate with a RADIUS server using 802.1X and the Extensible Authentication Protocol (EAP). It can be used for computers with wired or wireless LAN connections to complete a strong authentication before joining the network and supports the dynamic assignment of WEP keys.
Network Admission Control (NAC) refers to Cisco's version of Network Access Control, which restricts access to the network based on identity or security posture. When a network device is configured for NAC, it can force user or machine authentication prior to granting access to the network. In addition, guest access can be granted to a quarantine area for remediation of any problems that may have caused authentication failure. This is enforced through an inline custom network device, changes to an existing switch or router, or a restricted DHCP class. A typical (non-free) WiFi connection is a form of NAC. The user must present some sort of credentials before being granted access to the network.
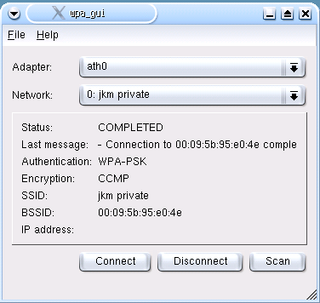
wpa_supplicant is a free software implementation of an IEEE 802.11i supplicant for Linux, FreeBSD, NetBSD, QNX, AROS, Microsoft Windows, Solaris, OS/2 and Haiku. In addition to being a fully featured WPA2 supplicant, it also implements WPA and older wireless LAN security protocols.

In computer networking, a supplicant is an entity at one end of a point-to-point LAN segment that seeks to be authenticated by an authenticator attached to the other end of that link. The IEEE 802.1X standard uses the term "supplicant" to refer either to hardware or to software. In practice, a supplicant is a software application installed on an end-user's computer. The user invokes the supplicant and submits credentials to connect the computer to a secure network. If the authentication succeeds, the authenticator typically allows the computer to connect to the network.
Devicescape develops client/server software services for wireless networking connectivity, analytics, and context-awareness. Founded in 2001 as Instant802 Networks, the company was renamed to Devicescape in January 2005. Devicescape is a venture backed private company.
A password manager is a computer program that allows users to store, generate, and manage their personal passwords for online services.
WISPr or Wireless Internet Service Provider roaming is a draft protocol submitted to the Wi-Fi Alliance that allows users to roam between wireless internet service providers in a fashion similar to that which allows cellphone users to roam between carriers. A RADIUS server is used to authenticate the subscriber's credentials.
AEGIS SecureConnect is the former name of a network authentication system used in IEEE 802.1X networks. It was developed by Meetinghouse Data Communications, Inc.; the system was renamed "Cisco Secure Services Client" when Meetinghouse was acquired by Cisco Systems. The AEGIS Protocol is an 802.1X supplicant, and is commonly installed along with a Network Interface Card's (NIC) or VPN drivers.

In computer security, logging in is the process by which an individual gains access to a computer system by identifying and authenticating themselves. The user credentials are typically some form of "username" and a matching "password", and these credentials themselves are sometimes referred to as a login. In practice, modern secure systems often require a second factor such as email or SMS confirmation for extra security.

Wireless@SG is a wireless broadband programme developed by the Infocomm Development Authority (IDA) of Singapore as part of its Next Generation National Infocomm Infrastructure initiative, being part of the nation's 10-year masterplan called Intelligent Nation 2015 (iN2015).
Funk Software was a US-based company that was acquired by Juniper Networks in 2005 for US$ 122 million. The company was founded in 1982 by Paul Funk, and was headquartered in Cambridge, Massachusetts.
Social login is a form of single sign-on using existing information from a social networking service such as Facebook, Twitter or Google, to sign into a third party website instead of creating a new login account specifically for that website. It is designed to simplify logins for end users as well as provide more and more reliable demographic information to web developers.
The Wireless Broadband Alliance (WBA) is an industry association formed to promote interoperability between operators in the Wi-Fi industry, with the stated aim of providing an excellent user experience. To achieve this, the WBA promotes interoperability initiatives including the Next Generation Hotspot (NGH), Wi-Fi Roaming and the WBA's Interoperability Compliance Program. The WBA runs the Wi-Fi Global Congress, an industry meeting. and hosts webinars to share best practice and advance knowledge.
Intuitive Password is a proprietary freemium password manager and secure digital wallet that stores users' passwords and confidential data. It was launched in 2013 by the Australian company Intuitive Security Systems. Intuitive Password received mixed reviews. Neil J. Rubeking wrote in PC Magazine in 2013 that Intuitive Password's not having automated password capture like some of its competitors was a significant downside.
References
- ↑ "Wireless Authentication Implementation (Windows CE)". microsoft.com. Retrieved 2008-03-18.
| This article about wireless technology is a stub. You can help Wikipedia by expanding it. |
| This network-related software article is a stub. You can help Wikipedia by expanding it. |