Cryptanalysis refers to the process of analyzing information systems in order to understand hidden aspects of the systems. Cryptanalysis is used to breach cryptographic security systems and gain access to the contents of encrypted messages, even if the cryptographic key is unknown.

Colossus was a set of computers developed by British codebreakers in the years 1943–1945 to help in the cryptanalysis of the Lorenz cipher. Colossus used thermionic valves to perform Boolean and counting operations. Colossus is thus regarded as the world's first programmable, electronic, digital computer, although it was programmed by switches and plugs and not by a stored program.

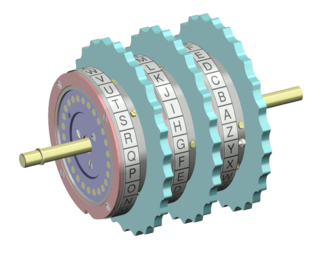
The Enigma machine is a cipher device developed and used in the early- to mid-20th century to protect commercial, diplomatic, and military communication. It was employed extensively by Nazi Germany during World War II, in all branches of the German military. The Enigma machine was considered so secure that it was used to encipher the most top-secret messages.

A stream cipher is a symmetric key cipher where plaintext digits are combined with a pseudorandom cipher digit stream (keystream). In a stream cipher, each plaintext digit is encrypted one at a time with the corresponding digit of the keystream, to give a digit of the ciphertext stream. Since encryption of each digit is dependent on the current state of the cipher, it is also known as state cipher. In practice, a digit is typically a bit and the combining operation is an exclusive-or (XOR).

In the history of cryptography, the "System 97 Typewriter for European Characters" (九七式欧文印字機) or "Type B Cipher Machine", codenamed Purple by the United States, was an encryption machine used by the Japanese Foreign Office from February 1939 to the end of World War II. The machine was an electromechanical device that used stepping-switches to encrypt the most sensitive diplomatic traffic. All messages were written in the 26-letter English alphabet, which was commonly used for telegraphy. Any Japanese text had to be transliterated or coded. The 26-letters were separated using a plug board into two groups, of six and twenty letters respectively. The letters in the sixes group were scrambled using a 6 × 25 substitution table, while letters in the twenties group were more thoroughly scrambled using three successive 20 × 25 substitution tables.

In the history of cryptography, the ECM Mark II was a cipher machine used by the United States for message encryption from World War II until the 1950s. The machine was also known as the SIGABA or Converter M-134 by the Army, or CSP-888/889 by the Navy, and a modified Navy version was termed the CSP-2900.
In cryptography, a block cipher mode of operation is an algorithm that uses a block cipher to provide information security such as confidentiality or authenticity. A block cipher by itself is only suitable for the secure cryptographic transformation of one fixed-length group of bits called a block. A mode of operation describes how to repeatedly apply a cipher's single-block operation to securely transform amounts of data larger than a block.

William Frederick Friedman was a US Army cryptographer who ran the research division of the Army's Signal Intelligence Service (SIS) in the 1930s, and parts of its follow-on services into the 1950s. In 1940, subordinates of his led by Frank Rowlett broke Japan's PURPLE cipher, thus disclosing Japanese diplomatic secrets before America's entrance into World War II.
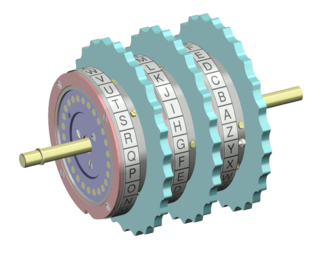
In cryptography, a rotor machine is an electro-mechanical stream cipher device used for encrypting and decrypting messages. Rotor machines were the cryptographic state-of-the-art for a prominent period of history; they were in widespread use in the 1920s–1970s. The most famous example is the German Enigma machine, the output of which was deciphered by the Allies during World War II, producing intelligence code-named Ultra.

The Lorenz SZ40, SZ42a and SZ42b were German rotor stream cipher machines used by the German Army during World War II. They were developed by C. Lorenz AG in Berlin. The model name SZ was derived from Schlüssel-Zusatz, meaning cipher attachment. The instruments implemented a Vernam stream cipher.

The Siemens & Halske T52, also known as the Geheimschreiber, or Schlüsselfernschreibmaschine (SFM), was a World War II German cipher machine and teleprinter produced by the electrical engineering firm Siemens & Halske. The instrument and its traffic were codenamed Sturgeon by British cryptanalysts.

The bombe was an electro-mechanical device used by British cryptologists to help decipher German Enigma-machine-encrypted secret messages during World War II. The US Navy and US Army later produced their own machines to the same functional specification, albeit engineered differently both from each other and from Polish and British bombes.

In cryptography, the avalanche effect is the desirable property of cryptographic algorithms, typically block ciphers and cryptographic hash functions, wherein if an input is changed slightly, the output changes significantly. In the case of high-quality block ciphers, such a small change in either the key or the plaintext should cause a drastic change in the ciphertext. The actual term was first used by Horst Feistel, although the concept dates back to at least Shannon's diffusion.
Cryptography was used extensively during World War II because of the importance of radio communication and the ease of radio interception. The nations involved fielded a plethora of code and cipher systems, many of the latter using rotor machines. As a result, the theoretical and practical aspects of cryptanalysis, or codebreaking, were much advanced.

The TSEC/KL-7, also known as Adonis was an off-line non-reciprocal rotor encryption machine. The KL-7 had rotors to encrypt the text, most of which moved in a complex pattern, controlled by notched rings. The non-moving rotor was fourth from the left of the stack. The KL-7 also encrypted the message indicator.
In the history of cryptography, the NEMA , also designated the T-D (Tasten-Druecker-Maschine), was a 10-wheel rotor machine designed by the Swiss Army during the World War II as a replacement for their Enigma machines.

In cryptography, Fialka (M-125) is the name of a Cold War-era Soviet cipher machine. A rotor machine, the device uses 10 rotors, each with 30 contacts along with mechanical pins to control stepping. It also makes use of a punched card mechanism. Fialka means "violet" in Russian. Information regarding the machine was quite scarce until c. 2005 because the device had been kept secret.
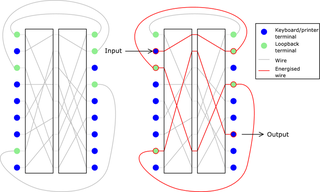
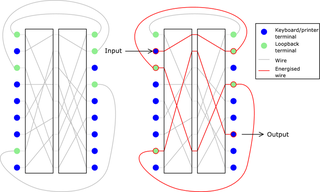
The HX-63 was an advanced rotor machine designed by Crypto AG founder Boris Hagelin. Development of the device started in 1952 and lasted a decade. The machine had nine rotors, each with 41 contacts. There were 26 keyboard inputs and outputs, leaving 15 wires to "loop back" through the rotors via a different path. Moreover, each rotor wire could be selected from one of two paths. The movement of the rotors was irregular and controlled by switches. There were two plugboards with the machine; one to scramble the input, and one for the loop-back wires. The machine also used a technique called reinjection (also called reentry), which increased its security exponentially. The machine could be set up in around 10600 different configurations.
In cryptography, a distinguishing attack is any form of cryptanalysis on data encrypted by a cipher that allows an attacker to distinguish the encrypted data from random data. Modern symmetric-key ciphers are specifically designed to be immune to such an attack. In other words, modern encryption schemes are pseudorandom permutations and are designed to have ciphertext indistinguishability. If an algorithm is found that can distinguish the output from random faster than a brute force search, then that is considered a break of the cipher.

In the history of cryptography, 91-shiki ōbun injiki or Angōki Taipu-A, codenamed Red by the United States, was a diplomatic cryptographic machine used by the Japanese Foreign Office before and during World War II. A relatively simple device, it was quickly broken by western cryptographers. The Red cipher was succeeded by the Type B "Purple" machine which used some of the same principles. Parallel usage of the two systems assisted in the breaking of the Purple system.