A password, sometimes called a passcode, is secret data, typically a string of characters, usually used to confirm a user's identity. Traditionally, passwords were expected to be memorized, but the large number of password-protected services that a typical individual accesses can make memorization of unique passwords for each service impractical. Using the terminology of the NIST Digital Identity Guidelines, the secret is held by a party called the claimant while the party verifying the identity of the claimant is called the verifier. When the claimant successfully demonstrates knowledge of the password to the verifier through an established authentication protocol, the verifier is able to infer the claimant's identity.
Single sign-on (SSO) is an authentication scheme that allows a user to log in with a single ID to any of several related, yet independent, software systems.
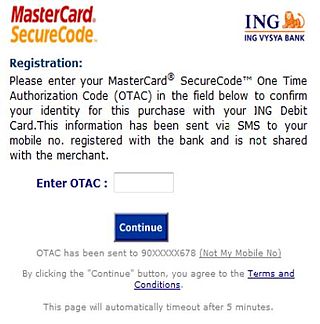
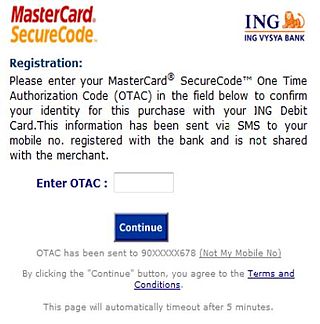
A one-time password (OTP), also known as a one-time PIN, one-time passcode, one-time authorization code (OTAC) or dynamic password, is a password that is valid for only one login session or transaction, on a computer system or other digital device. OTPs avoid several shortcomings that are associated with traditional (static) password-based authentication; a number of implementations also incorporate two-factor authentication by ensuring that the one-time password requires access to something a person has as well as something a person knows.

OpenID is an open standard and decentralized authentication protocol promoted by the non-profit OpenID Foundation. It allows users to be authenticated by co-operating sites using a third-party identity provider (IDP) service, eliminating the need for webmasters to provide their own ad hoc login systems, and allowing users to log in to multiple unrelated websites without having to have a separate identity and password for each. Users create accounts by selecting an OpenID identity provider, and then use those accounts to sign on to any website that accepts OpenID authentication. Several large organizations either issue or accept OpenIDs on their websites.

Keychain is a password management system developed by Apple for macOS. It was introduced with Mac OS 8.6, and was included in all subsequent versions of the operating system, as well as in iOS. A keychain can contain various types of data: passwords, private keys, certificates, and secure notes. Some data, primarily passwords, in the Keychain are visible and editable using a user-friendly interface in Passwords, a built in app in macOS Sequoia and iOS 18 and available in System Settings/Settings in earlier versions of Apple's operating systems.

Password strength is a measure of the effectiveness of a password against guessing or brute-force attacks. In its usual form, it estimates how many trials an attacker who does not have direct access to the password would need, on average, to guess it correctly. The strength of a password is a function of length, complexity, and unpredictability.
A password manager is a computer program that allows users to store and manage their passwords for local applications or online services such as web applications, online shops or social media. A web browser generally has a built in version of a password manager. These have been criticized frequently as many have stored the passwords in plaintext, allowing hacking attempts.
A Google Account is a user account that is required for access, authentication and authorization to certain online Google services. It is also often used as single sign-on for third party services.
Password fatigue is the feeling experienced by many people who are required to remember an excessive number of passwords as part of their daily routine, such as to log in to a computer at work, undo a bicycle lock or conduct banking from an automated teller machine. The concept is also known as password chaos, or more broadly as identity chaos.
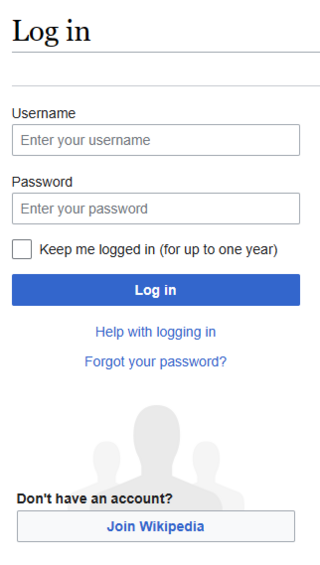
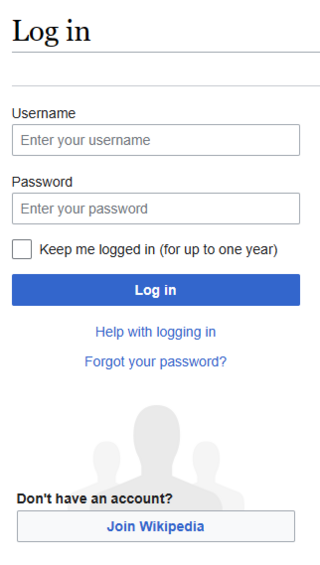
In computer security, logging in is the process by which an individual gains access to a computer system or program by identifying and authenticating themselves.

Multi-factor authentication is an electronic authentication method in which a user is granted access to a website or application only after successfully presenting two or more pieces of evidence to an authentication mechanism. MFA protects personal data—which may include personal identification or financial assets—from being accessed by an unauthorized third party that may have been able to discover, for example, a single password.

Google Authenticator is a software-based authenticator by Google. It implements multi-factor authentication services using the time-based one-time password and HMAC-based one-time password, for authenticating users of software applications.

1Password is a password manager developed by the Canadian software company AgileBits Inc. It supports multiple platforms such as iOS, Android, Windows, Linux, and macOS. It provides a place for users to store various passwords, software licenses, and other sensitive information in a virtual vault that is locked with a PBKDF2-guarded master password. By default, the user’s encrypted vault is hosted on AgileBits’ servers for a monthly fee.

Chrome Remote Desktop is a remote desktop software tool, developed by Google, that allows a user to remotely control another computer's desktop through a proprietary protocol also developed by Google, internally called Chromoting. The protocol transmits the keyboard and mouse events from the client to the server, relaying the graphical screen updates back in the other direction over a computer network. This feature, therefore, consists of a server component for the host computer, and a client component on the computer accessing the remote server. Chrome Remote Desktop uses a unique protocol, as opposed to using the common Remote Desktop Protocol.

SQRL or Secure, Quick, Reliable Login is a draft open standard for secure website login and authentication. The software typically uses a link of the scheme sqrl:// or optionally a QR code, where a user identifies via a pseudonymous zero-knowledge proof rather than providing a user ID and password. This method is thought to be impervious to a brute-force password attack or data breach. It shifts the burden of security away from the party requesting the authentication and closer to the operating-system implementation of what is possible on the hardware, as well as to the user. SQRL was proposed by Steve Gibson of Gibson Research Corporation in October 2013 as a way to simplify the process of authentication without the risk of revelation of information about the transaction to a third party.
Nitrokey is an open-source USB key used to enable the secure encryption and signing of data. The secret keys are always stored inside the Nitrokey which protects against malware and attackers. A user-chosen PIN and a tamper-proof smart card protect the Nitrokey in case of loss and theft. The hardware and software of Nitrokey are open-source. The free software and open hardware enables independent parties to verify the security of the device. Nitrokey is supported on Microsoft Windows, macOS, Linux, and BSD.
Credential stuffing is a type of cyberattack in which the attacker collects stolen account credentials, typically consisting of lists of usernames or email addresses and the corresponding passwords, and then uses the credentials to gain unauthorized access to user accounts on other systems through large-scale automated login requests directed against a web application. Unlike credential cracking, credential stuffing attacks do not attempt to use brute force or guess any passwords – the attacker simply automates the logins for a large number of previously discovered credential pairs using standard web automation tools such as Selenium, cURL, PhantomJS or tools designed specifically for these types of attacks, such as Sentry MBA, SNIPR, STORM, Blackbullet and Openbullet.
Intuitive Password is a proprietary freemium password manager and secure digital wallet that stores users' passwords and confidential data. It was launched in 2013 by the Australian company Intuitive Security Systems. Intuitive Password received mixed reviews. Neil J. Rubeking wrote in PC Magazine in 2013 that one significant downside of Intuitive Password's was their lack of automated password capture, like some of their competitors.
Web Authentication (WebAuthn) is a web standard published by the World Wide Web Consortium (W3C). WebAuthn is a core component of the FIDO2 Project under the guidance of the FIDO Alliance. The goal of the project is to standardize an interface for authenticating users to web-based applications and services using public-key cryptography. WebAuthn credentials that are available across multiple devices are commonly referred to as passkeys.

Passwordless authentication is an authentication method in which a user can log in to a computer system without entering a password or any other knowledge-based secret. In most common implementations users are asked to enter their public identifier and then complete the authentication process by providing a secure proof of identity through a registered device or token.