Related Research Articles

The National Security Agency (NSA) is an intelligence agency of the United States Department of Defense, under the authority of the Director of National Intelligence (DNI). The NSA is responsible for global monitoring, collection, and processing of information and data for foreign and domestic intelligence and counterintelligence purposes, specializing in a discipline known as signals intelligence (SIGINT). The NSA is also tasked with the protection of U.S. communications networks and information systems. The NSA relies on a variety of measures to accomplish its mission, the majority of which are clandestine. The NSA has roughly 32,000 employees.

MUSCULAR (DS-200B), located in the United Kingdom, is the name of a surveillance program jointly operated by Britain's Government Communications Headquarters (GCHQ) and the U.S. National Security Agency (NSA) that was revealed by documents released by Edward Snowden and interviews with knowledgeable officials. GCHQ is the primary operator of the program. GCHQ and the NSA have secretly broken into the main communications links that connect the data centers of Yahoo! and Google. Substantive information about the program was made public at the end of October 2013.

Laura Poitras is an American director and producer of documentary films.

The Utah Data Center (UDC), also known as the Intelligence Community Comprehensive National Cybersecurity Initiative Data Center, is a data storage facility for the United States Intelligence Community that is designed to store data estimated to be on the order of exabytes or larger. Its purpose is to support the Comprehensive National Cybersecurity Initiative (CNCI), though its precise mission is classified. The National Security Agency (NSA) leads operations at the facility as the executive agent for the Director of National Intelligence. It is located at Camp Williams near Bluffdale, Utah, between Utah Lake and Great Salt Lake and was completed in May 2014 at a cost of $1.5 billion.

PRISM is a code name for a program under which the United States National Security Agency (NSA) collects internet communications from various U.S. internet companies. The program is also known by the SIGAD US-984XN. PRISM collects stored internet communications based on demands made to internet companies such as Google LLC and Apple under Section 702 of the FISA Amendments Act of 2008 to turn over any data that match court-approved search terms. Among other things, the NSA can use these PRISM requests to target communications that were encrypted when they traveled across the internet backbone, to focus on stored data that telecommunication filtering systems discarded earlier, and to get data that is easier to handle.

Boundless Informant is a big data analysis and data visualization tool used by the United States National Security Agency (NSA). It gives NSA managers summaries of the NSA's worldwide data collection activities by counting metadata. The existence of this tool was disclosed by documents leaked by Edward Snowden, who worked at the NSA for the defense contractor Booz Allen Hamilton. Those disclosed documents were in a direct contradiction to the NSA's assurance to United States Congress that it does not collect any type of data on millions of Americans.
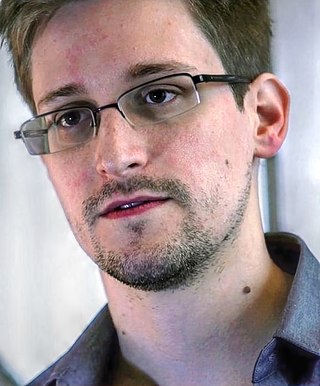
Edward Joseph Snowden is an American and naturalized Russian citizen who was a computer intelligence consultant and whistleblower who leaked highly classified information from the National Security Agency (NSA) in 2013 when he was an employee and subcontractor. His disclosures revealed numerous global surveillance programs, many run by the NSA and the Five Eyes intelligence alliance with the cooperation of telecommunication companies and European governments and prompted a cultural discussion about national security and individual privacy.

Fairview is a secret program under which the National Security Agency cooperates with the American telecommunications company AT&T in order to collect phone, internet and e-mail data mainly of foreign countries' citizens at major cable landing stations and switching stations inside the United States. The FAIRVIEW program started in 1985, one year after the Bell breakup.

XKeyscore is a secret computer system used by the United States National Security Agency (NSA) for searching and analyzing global Internet data, which it collects in real time. The NSA has shared XKeyscore with other intelligence agencies, including the Australian Signals Directorate, Canada's Communications Security Establishment, New Zealand's Government Communications Security Bureau, Britain's Government Communications Headquarters, Japan's Defense Intelligence Headquarters, and Germany's Bundesnachrichtendienst.
The Unified Targeting Tool (UTT) is a software program used by NSA to select targets for surveillance. It has gained attention as one of the programs exposed by Edward Snowden. It is mentioned as part of the PRISM program, and in other documents.

BLARNEY is a communications surveillance program of the National Security Agency (NSA) of the United States. It started in 1978, operated under the Foreign Intelligence Surveillance Act and was expanded after the September 11 attacks.

The practice of mass surveillance in the United States dates back to wartime monitoring and censorship of international communications from, to, or which passed through the United States. After the First and Second World Wars, mass surveillance continued throughout the Cold War period, via programs such as the Black Chamber and Project SHAMROCK. The formation and growth of federal law-enforcement and intelligence agencies such as the FBI, CIA, and NSA institutionalized surveillance used to also silence political dissent, as evidenced by COINTELPRO projects which targeted various organizations and individuals. During the Civil Rights Movement era, many individuals put under surveillance orders were first labelled as integrationists, then deemed subversive, and sometimes suspected to be supportive of the communist model of the United States' rival at the time, the Soviet Union. Other targeted individuals and groups included Native American activists, African American and Chicano liberation movement activists, and anti-war protesters.
During the 2010s, international media news reports revealed new operational details about the Anglophone cryptographic agencies' global surveillance of both foreign and domestic nationals. The reports mostly relate to top secret documents leaked by ex-NSA contractor Edward Snowden. The documents consist of intelligence files relating to the U.S. and other Five Eyes countries. In June 2013, the first of Snowden's documents were published, with further selected documents released to various news outlets through the year.
This is a category of disclosures related to global surveillance.
Global mass surveillance can be defined as the mass surveillance of entire populations across national borders.

This timeline of global surveillance disclosures from 2013 to the present day is a chronological list of the global surveillance disclosures that began in 2013. The disclosures have been largely instigated by revelations from the former American National Security Agency contractor Edward Snowden.

MYSTIC is a former secret program used since 2009 by the US National Security Agency (NSA) to collect the metadata as well as the content of phone calls from several countries. The program was first revealed in March 2014, based upon documents leaked by Edward Snowden.
The United States is widely considered to have one of the most extensive and sophisticated intelligence network of any nation in the world, with organizations including the Central Intelligence Agency and the National Security Agency, amongst others. It has conducted numerous espionage operations against foreign countries, including both allies and rivals. Its operations have included the use of industrial espionage, cyber espionage. and mass surveillance.
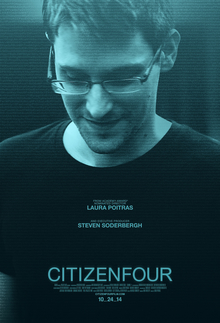
Citizenfour is a 2014 documentary film directed by Laura Poitras, concerning Edward Snowden and the NSA spying scandal. The film had its US premiere on October 10, 2014, at the New York Film Festival and its UK premiere on October 17, 2014, at the BFI London Film Festival. The film features Snowden and Glenn Greenwald, and was co-produced by Poitras, Mathilde Bonnefoy, and Dirk Wilutzky, with Steven Soderbergh and others serving as executive producers. Citizenfour received critical acclaim upon release, and was the recipient of numerous accolades, including Best Documentary Feature at the 87th Academy Awards. This film is the third part to a 9/11 trilogy following My Country, My Country (2006) and The Oath (2010).

RAMPART-A is the code name for global mass surveillance and world-wide signals intelligence partnership program led by the United States National Security Agency (NSA). Aim of the program is to "gain access to high-capacity international fiber-optic cables that transit at major congestion points around the world".
References
- ↑ Greenwald, Glenn; MacAskill, Ewen; Poitras, Laura; Ackerman, Spencer; Rushe, Dominic (July 11, 2013). "How Microsoft handed the NSA access to encrypted messages". The Guardian . Retrieved July 12, 2013.
- ↑ Gellman, Barton; Poitras, Laura (June 6, 2013). "US Intelligence Mining Data from Nine U.S. Internet Companies in Broad Secret Program". The Washington Post . Retrieved July 12, 2013.
- ↑ Greenwald, Glenn (2014). No Place to Hide. New York: Metropolitan Books. p. 102. ISBN 978-1-62779-161-8.
- ↑ "Edward Snowden, after months of NSA revelations, says his mission's accomplished" – The Washington Post, December 23, 2013.
- ↑ Top Level Telecommunications, Some numbers about NSA's data collection, June 5, 2014
