Objectives
PWS upholds the thesis that the Big Brother described in George Orwell's novel is gradually gaining form, passively and with silent acceptance by the people. It is gradually inserted into our lives through the false statement: "it is right to sacrifice one's privacy in exchange for greater security".
According to security experts such as Bruce Schneier, following events such as the SISMI-Telecom scandal, official bodies which monitor telecommunications are acquiring a de facto totalitarian power, whatever the official political situation. If the target is really to increase public security, the mere presence of monitoring agencies constitutes an element of insecurity.[ citation needed ]
Because of the ignorance of citizens regarding security, official agencies push for an ever increasing situation which damages human rights.[ vague ] PWS is engaged in spreading tools to protect users from such risk. Fortunately, those tools exist because the Internet is based upon open technologies.
Individual security can be achieved only by using preventive protection tools on private computers. It cannot be delegated to others such as Internet service providers.
PWS aims to increase the use of technologies such as data encryption and anonymity. This can be achieved by using programs written according to the guidelines of secure software, such as:
- the software in use (including the operating system) must be an open system, allowing the user, if so inclined and capable, to verify its effective behaviour.
- the cryptographic algorithms employed must be public. Only thus can the community perform a mathematical analysis (cryptanalysis) and a study of potential attacks, in order to achieve a continuous improvement.
If either of these conditions is missing, the software cannot be considered secure, as it is then based upon the concept of security through obscurity, which has never been proved a valid security paradigm. Events such as JAP, [2] PGP 5.x and 6.x [3] have shown the unreliability of this model.
To be consistent with the proposed technologies, the PWS website is not available on the Internet, but through Freenet, with the following key:
USK@RU-C2q5kN7K62WO3seMMjSTUY8izF2vCFyVFOnLf~Q0,wxvGO2QMT6IN9c7dNUhHeHnXVVwhq8YLbQL~DlMA7YE,AQACAAE/pws/3
A mirror is also available on the Internet to increase accessibility. [4]
To contact members of PWS conventional e-mail addresses are not used, but rather the nym alias ws@nym.panta-rhei.eu.org, whose PGP key is published on a keyserver. [5]
Project resources
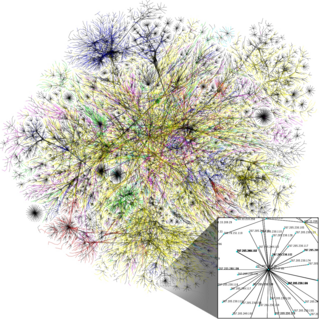
Anonymity in the network is guaranteed by the Mix-net technology, first studied by David Chaum in 1981. This technology requires that user resources be employed and shared in collaboration. The reciprocal sharing of resources through secure algorithms ensures that an attacker able to monitor the network passively (reading all traffic in all segments) or actively (generating arbitrary traffic) would be unable to discover the identities of individuals.
Software such as anonymous remailer, Tor and Freenet are based on these advanced concepts, and have evolved through the years.
The architecture of these networks is based on collaboration and availability of shared resources. As a start, groups of volunteers like PWS are making eight servers available, dedicated to the support of this network. [6]
Law proposal
At the 2005 annual convention organized by Bileta, [7] an association active since 1986 for the study of laws concerning the use of technology in Britain and Ireland, PWS presented a study concerning data retention. [8]
Data retention is the automatic collection of network data in support of investigative bodies and law enforcement. Before several reforms concerning security, it was necessary in some jurisdictions to possess a mandate by a judicial authority before collecting data to be used in investigations. With the decentralization of technologies due to the spread of Internet, many private bodies have been invested with the responsibility for data collection.
Such automatic data collection of Internet traffic is possible using freely available software, such as Wireshark or tcpdump, originally conceived to aid network technicians in debugging and maintenance.
Collection of personal data is forbidden in the European Union according to the principle of freedom of secrecy of correspondence. For this reason a law proposal has been investigated to regulate the collection of log and backup data, which would define which data are to be considered sensitive, and allowing technicians to perform maintenance operations, but at the same time preventing the unauthorized access to personal data by external parties. This law proposal was presented to the Italian Parliament by deputy Maurizio Turco in 2006. This law proposal was not accepted. Instead, the validity of the current Italian Law Decree 144/2005, due to expire on 31 December 2007, has been extended in time, to continue allowing the collection of personal data with a view to combating international terrorism.
E-Privacy conference
PWS organizes the annual E-Privacy conference, which is the first such Italian conference concerning aspects of privacy in the network. Contributions are given by both technical and law experts. This conference has been held in the Palazzo Vecchio in Florence, with the exception of the 2002 edition, which was hosted at the University of Florence.
Each edition has had a main theme:
- 2002: E-privacy, confidentiality and individual rights in the network, opposing Big Brother in the third millennium Topics covered: Italian Law 675/1996, political trends to pass laws reducing freedom in the net, Freenet, PGP/GPG, anonymous remailer and steganography.
- 2003: Defending identity and freedom of expression against requests for more security Topics treated included: data retention, TCPA, analysing threat models to define a minimum personal security standard, digital signatures, cryptography as a basic user defence tool.
- 2004: Data retention and the right to oblivion Topics included: data retention, RFID, the right to delete sensitive data, surveillance as an answer to terrorism, anonymous peer-to-peer (P2P) networking, abuses of video surveillance, decentralized technologies.
- 2005: Data retention and privacy in the network: darknet was considered, as well as presenting the P-Box project, then Free software, civil responsibilities and privacy violations, the OpenPGP standard, a law proposal to regulate automatic data collection, Biometry.
- 2006: The main theme was not set. Topics discussed were: spyware, trusted computing, DRM, possible misuses of electronic voting, dangers to privacy caused by search engines.
- 2007: Social control and technocontrol. Topics included: VOIP, personal identity and digital identity, accessibility, the Tanga articles and IT incidents.
The 2008 conference was hypothesized to be held on the 9th and 10 May in the Palazzo Vecchio located in Florence.
"e-privacy" is also the name of a mailing list. Its e-mail address is e-privacy@firenze.linux.it, subscription is free and archives are publicly available online. [9]
P-Box project
Anonymity technologies are based on collaborative groups of users who reciprocally choose to share their resources. These anonymous networks can be accessed even from devices with low computing power and low communications bandwidth. To help diffuse these technologies PWS has introduced P-Boxes [10] (Privacy Boxes), which are small and simple devices to help protect privacy.
Three models have been developed:
- P-Box Model I: a modified Xbox, with the Linux operating system, running standard services and the Mixminion remailer.
- P-Box Model II: a PC Soekris 4501, with the Linux operating system, running Mixminion, TOR, Mixmaster and the Postfix mail server.
- P-Box Model III: based on a Soekris 4801, it includes the same applications as model II. It can also be used as access point and includes the e-mail server protocols IMAP and POP3.
Big Brother Awards (Italian section)
Big Brother Awards (BBA) is an initiative of Privacy International with the motto "watching the watchman worldwide". PWS manages the polling and award assignation to the Italian bodies with the worst performance in the field of human rights. Several categories exist, according to the rights violation achieved:
- Lifelong threat: the body or agency which has caused most damage to privacy throughout its existence.
- Worst public agency: given to the public agency (government institution, public body, authority, etc.) which caused most damage to privacy in the current year.
- Worst private enterprise: awarded to private or corporate institutions with the worst privacy record in the current year.
- Most invasive technology: the technology with the worst impact on privacy.
- Boot mouth: the "best" (most terrifying, ridiculous, erroneous, falsely tranquillizing) statement said or printed about privacy in the current year.
- People's lament: who received most votes, also in different categories.
Project 95%
This section is written like a personal reflection, personal essay, or argumentative essay that states a Wikipedia editor's personal feelings or presents an original argument about a topic.(August 2010) |
Project 95% (Ninety Five Percent – No False Privacy) is a project advocating awareness in Internet issues. The Internet was born as a free and decentralized network, but its most common use relies on a few centralized services. A blatant example is the number of users who are increasingly more dependent on webmail services such as Gmail, Hotmail and Yahoo! Mail. Even though there is an understandable tendency favouring ease of use, as the customers can access their services from disparate locations, the downside is the vast usage of profiling instruments on the part of free service providers, with the view of providing more targeted web marketing.
It is not PWS's intention to tag any specific commercial service as a danger to privacy, but to point out that a greater confidentiality can be achieved using individual mail servers, private webmail programs, privately owned domains.
This is perfectly achievable using freely available software and their configuration can be automated even for non technically competent users.
95% is the percentage of reliability of a home based server, connected to the Internet through a flat ADSL line, to demonstrate that it is not necessary to employ the offerings of centralized enterprises to obtain good services. Hence the NFP project, which informs on the technical possibilities that a modern computer can offer, to connect to the Internet fully and without undue effort on the part of the user.
The P-Box is an example of a technological answer to these necessities.