Authentication is the act of proving an assertion, such as the identity of a computer system user. In contrast with identification, the act of indicating a person or thing's identity, authentication is the process of verifying that identity. It might involve validating personal identity documents, verifying the authenticity of a website with a digital certificate, determining the age of an artifact by carbon dating, or ensuring that a product or document is not counterfeit.

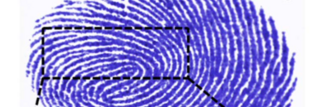
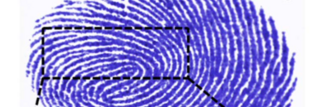
A fingerprint is an impression left by the friction ridges of a human finger. The recovery of partial fingerprints from a crime scene is an important method of forensic science. Moisture and grease on a finger result in fingerprints on surfaces such as glass or metal. Deliberate impressions of entire fingerprints can be obtained by ink or other substances transferred from the peaks of friction ridges on the skin to a smooth surface such as paper. Fingerprint records normally contain impressions from the pad on the last joint of fingers and thumbs, though fingerprint cards also typically record portions of lower joint areas of the fingers.
Biometrics are body measurements and calculations related to human characteristics and features. Biometric authentication is used in computer science as a form of identification and access control. It is also used to identify individuals in groups that are under surveillance.
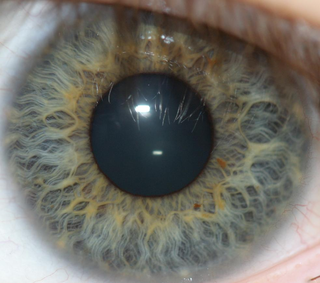
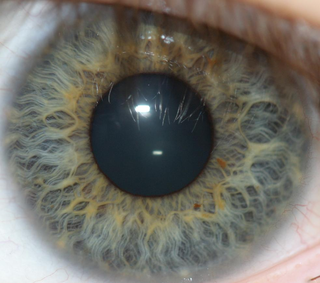
Iris recognition is an automated method of biometric identification that uses mathematical pattern-recognition techniques on video images of one or both of the irises of an individual's eyes, whose complex patterns are unique, stable, and can be seen from some distance. The discriminating powers of all biometric technologies depend on the amount of entropy they are able to encode and use in matching. Iris recognition is exceptional in this regard, enabling the avoidance of "collisions" even in cross-comparisons across massive populations. Its major limitation is that image acquisition from distances greater than a meter or two, or without cooperation, can be very difficult. However, the technology is in development and iris recognition can be accomplished from even up to 10 meters away or in a live camera feed.

A security token is a peripheral device used to gain access to an electronically restricted resource. The token is used in addition to, or in place of, a password. Examples of security tokens include wireless key cards used to open locked doors, a banking token used as a digital authenticator for signing in to online banking, or signing transactions such as wire transfers.
Logical security consists of software safeguards for an organization's systems, including user identification and password access, authenticating, access rights and authority levels. These measures are to ensure that only authorized users are able to perform actions or access information in a network or a workstation. It is a subset of computer security.
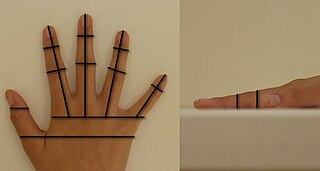
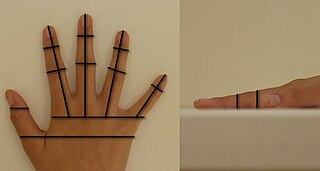
Hand geometry is a biometric that identifies users from the shape of their hands. Hand geometry readers measure a user's palm and fingers along many dimensions including length, width, deviation, and angle and compare those measurements to measurements stored in a file.
Living in the intersection of cryptography and psychology, password psychology is the study of what makes passwords or cryptographic keys easy to remember or guess.
A card reader is a data input device that reads data from a card-shaped storage medium and provides the data to a computer. Card readers can acquire data from a card via a number of methods, including: optical scanning of printed text or barcodes or holes on punched cards, electrical signals from connections made or interrupted by a card's punched holes or embedded circuitry, or electronic devices that can read plastic cards embedded with either a magnetic strip, computer chip, RFID chip, or another storage medium.
Password fatigue is the feeling experienced by many people who are required to remember an excessive number of passwords as part of their daily routine, such as to log in to a computer at work, undo a bicycle lock or conduct banking from an automated teller machine. The concept is also known as password chaos, or more broadly as identity chaos.
Vein matching, also called vascular technology, is a technique of biometric identification through the analysis of the patterns of blood vessels visible from the surface of the skin. Though used by the Federal Bureau of Investigation and the Central Intelligence Agency, this method of identification is still in development and has not yet been universally adopted by crime labs as it is not considered as reliable as more established techniques, such as fingerprinting. However, it can be used in conjunction with existing forensic data in support of a conclusion.
Cyber crime, or computer crime, refers to any crime that involves a computer and a network. The computer may have been used in the commission of a crime, or it may be the target. Netcrime refers, more precisely, to criminal exploitation of the Internet. Issues surrounding this type of crime have become high-profile, particularly those surrounding hacking, copyright infringement, identity theft, child pornography, and child grooming. There are also problems of privacy when confidential information is lost or intercepted, lawfully or otherwise.
A whole new range of techniques has been developed to identify people since the 1960s from the measurement and analysis of parts of their bodies to DNA profiles. Forms of identification are used to ensure that citizens are eligible for rights to benefits and to vote without fear of impersonation while private individuals have used seals and signatures for centuries to lay claim to real and personal estate. Generally, the amount of proof of identity that is required to gain access to something is proportionate to the value of what is being sought. It is estimated that only 4% of online transactions use methods other than simple passwords. Security of systems resources generally follows a three-step process of identification, authentication and authorization. Today, a high level of trust is as critical to eCommerce transactions as it is to traditional face-to-face transactions.
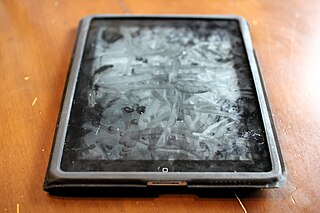
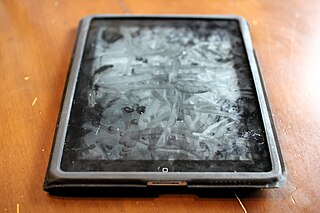
A smudge attack is an information extraction attack that discerns the password input of a touchscreen device such as a smartphone or tablet computer from fingerprint smudges. A team of researchers at the University of Pennsylvania were the first to investigate this type of attack in 2010. An attack occurs when an unauthorized user is in possession or is nearby the device of interest. The attacker relies on detecting the oily smudges produced and left behind by the user's fingers to find the pattern or code needed to access the device and its contents. Simple cameras, lights, fingerprint powder, and image processing software can be used to capture the fingerprint deposits created when the user unlocks their device. Under proper lighting and camera settings, the finger smudges can be easily detected, and the heaviest smudges can be used to infer the most frequent input swipes or taps from the user.
Biometrics are used by the South African government to combat fraud and corruption and to increase the efficiency of service delivery to the public.

Touch ID is an electronic fingerprint recognition feature designed and released by Apple Inc. that allows users to unlock devices, make purchases in the various Apple digital media stores, and authenticate Apple Pay online or in apps. It can also be used to lock and unlock password-protected notes on iPhone and iPad. Touch ID was first introduced in iPhones with the iPhone 5s in 2013. In 2015, Apple introduced a faster second-generation Touch ID in the iPhone 6s; a year later in 2016, it made its laptop debut in the MacBook Pro integrated on the right side of the Touch Bar. Touch ID has been used on all iPads since the iPad Air 2 was introduced in 2014. In MacBooks, each user account can have up to three fingerprints, and a total of five fingerprints across the system. Fingerprint information is stored locally in a secure enclave on the Apple A7 and later chips, not in the cloud, a design choice intended to secure fingerprint information from users or malicious attackers.
Eye vein verification is a method of biometric authentication that applies pattern-recognition techniques to video images of the veins in a user's eyes. The complex and random patterns are unique, and modern hardware and software can detect and differentiate those patterns at some distance from the eyes.
Identity-based security is a type of security that focuses on access to digital information or services based on the authenticated identity of an entity. It ensures that the users and services of these digital resources are entitled to what they receive. The most common form of identity-based security involves the login of an account with a username and password. However, recent technology has evolved into fingerprinting or facial recognition.
Biometric tokenization is the process of substituting a stored biometric template with a non-sensitive equivalent, called a token, that lacks extrinsic or exploitable meaning or value. The process combines the biometrics with public-key cryptography to enable the use of a stored biometric template for secure or strong authentication to applications or other systems without presenting the template in its original, replicable form.
Web Authentication (WebAuthn) is a web standard published by the World Wide Web Consortium (W3C). WebAuthn is a core component of the FIDO2 Project under the guidance of the FIDO Alliance. The goal of the project is to standardize an interface for authenticating users to web-based applications and services using public-key cryptography. WebAuthn credentials that are available across multiple devices are commonly referred to as passkeys.