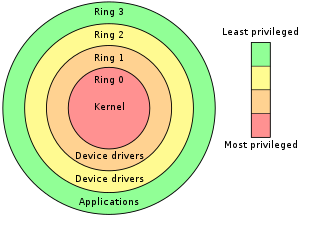
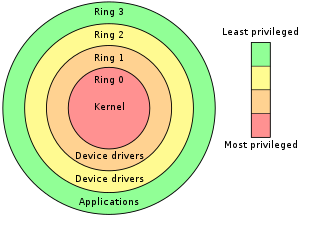
A rootkit is a collection of computer software, typically malicious, designed to enable access to a computer or an area of its software that is not otherwise allowed and often masks its existence or the existence of other software. The term rootkit is a compound of "root" and the word "kit". The term "rootkit" has negative connotations through its association with malware.

UEFI is a set of specifications written by the UEFI Forum. They define the architecture of the platform firmware used for booting and its interface for interaction with the operating system. Examples of firmware that implement these specifications are AMI Aptio, Phoenix SecureCore, TianoCore EDK II, InsydeH2O. UEFI replaces the BIOS which was present in the boot ROM of all personal computers that are IBM PC-compatible, although it can provide backwards compatibility with the BIOS using CSM booting. Intel developed the original Extensible Firmware Interface (EFI) specifications. Some of the EFI's practices and data formats mirror those of Microsoft Windows. In 2005, UEFI deprecated EFI 1.10.
The Advanced Host Controller Interface (AHCI) is a technical standard defined by Intel that specifies the register-level interface of Serial ATA (SATA) host controllers in a non-implementation-specific manner in its motherboard chipsets.
The Direct Rendering Manager (DRM) is a subsystem of the Linux kernel responsible for interfacing with GPUs of modern video cards. DRM exposes an API that user-space programs can use to send commands and data to the GPU and perform operations such as configuring the mode setting of the display. DRM was first developed as the kernel-space component of the X Server Direct Rendering Infrastructure, but since then it has been used by other graphic stack alternatives such as Wayland and standalone applications and libraries such as SDL2 and Kodi.

coreboot, formerly known as LinuxBIOS, is a software project aimed at replacing proprietary firmware found in most computers with a lightweight firmware designed to perform only the minimum number of tasks necessary to load and run a modern 32-bit or 64-bit operating system.

A free and open-source graphics device driver is a software stack which controls computer-graphics hardware and supports graphics-rendering application programming interfaces (APIs) and is released under a free and open-source software license. Graphics device drivers are written for specific hardware to work within a specific operating system kernel and to support a range of APIs used by applications to access the graphics hardware. They may also control output to the display if the display driver is part of the graphics hardware. Most free and open-source graphics device drivers are developed by the Mesa project. The driver is made up of a compiler, a rendering API, and software which manages access to the graphics hardware.

A Hackintosh is a computer that runs Apple's Macintosh operating system macOS on computer hardware not authorized for the purpose by Apple. This can also include running Macintosh software on hardware it is not originally authorized for. "Hackintoshing" began as a result of Apple's 2005 transition to Intel processors, away from PowerPC. Since 2005, Mac computers use the same x86-64 computer architecture as many other desktop PCs, laptops, and servers, meaning that in principle, the code making up macOS systems and software can be run on alternative platforms with minimal compatibility issues. Benefits cited for "Hackintoshing" can include cost, ease of repair and piecemeal upgrade, and freedom to use customized choices of components that are not available in the branded Apple products. macOS can also be run on several non-Apple virtualization platforms, although such systems are not usually described as Hackintoshes. Hackintosh laptops are sometimes referred to as "Hackbooks".

The Apple–Intel architecture, or Mactel, is an unofficial name used for Macintosh personal computers developed and manufactured by Apple Inc. that use Intel x86 processors, rather than the PowerPC and Motorola 68000 ("68k") series processors used in their predecessors or the ARM-based Apple silicon SoCs used in their successors. With the change in architecture, a change in firmware became necessary; Apple selected the Intel-designed Extensible Firmware Interface (EFI) as its comparable component to the Open Firmware used on its PowerPC architectures, and as the firmware-based replacement for the PC BIOS from Intel. With the change in processor architecture to x86, Macs gained the ability to boot into x86-native operating systems, while Intel VT-x brought near-native virtualization with macOS as the host OS.

The EFIsystem partition or ESP is a partition on a data storage device that is used by computers having the Unified Extensible Firmware Interface (UEFI). When a computer is booted, UEFI firmware loads files stored on the ESP to start installing operating systems and various utilities.
In the context of free and open-source software, proprietary software only available as a binary executable is referred to as a blob or binary blob. The term usually refers to a device driver module loaded into the kernel of an open-source operating system, and is sometimes also applied to code running outside the kernel, such as system firmware images, microcode updates, or userland programs. The term blob was first used in database management systems to describe a collection of binary data stored as a single entity.

Intel Active Management Technology (AMT) is hardware and firmware for remote out-of-band management of select business computers, running on the Intel Management Engine, a microprocessor subsystem not exposed to the user, intended for monitoring, maintenance, updating, and repairing systems. Out-of-band (OOB) or hardware-based management is different from software-based management and software management agents.
Pre-boot authentication (PBA) or power-on authentication (POA) serves as an extension of the BIOS, UEFI or boot firmware and guarantees a secure, tamper-proof environment external to the operating system as a trusted authentication layer. The PBA prevents anything being read from the hard disk such as the operating system until the user has confirmed they have the correct password or other credentials including multi-factor authentication.
Rooting is the process by which users of Android devices can attain privileged control over various subsystems of the device, usually smartphones. Because Android is based on a modified version of the Linux kernel, rooting an Android device gives similar access to administrative (superuser) permissions as on Linux or any other Unix-like operating system such as FreeBSD or macOS.
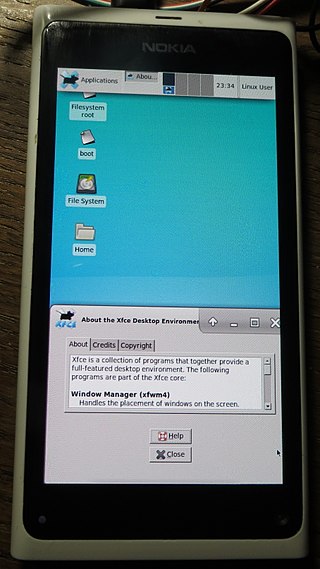
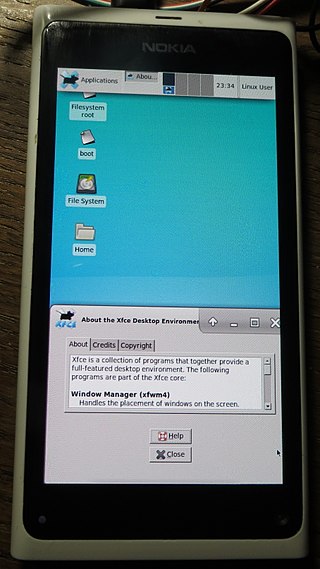
The hacking of consumer electronics is an increasingly common practice which users perform in order to customize and modify their devices beyond what is typically possible. This activity has a long history, dating from the days of early computer, programming, and electronics hobbyists.
A trusted execution environment (TEE) is a secure area of a main processor. It guarantees code and data loaded inside to be protected with respect to confidentiality and integrity. Data integrity prevents unauthorized entities from outside the TEE from altering data, while code integrity prevents code in the TEE from being replaced or modified by unauthorized entities, which may also be the computer owner itself as in certain DRM schemes described in SGX. This is done by implementing unique, immutable, and confidential architectural security such as Intel Software Guard Extensions which offers hardware-based memory encryption that isolates specific application code and data in memory. Intel SGX allows user-level code to allocate private regions of memory, called enclaves, which are designed to be protected from processes running at higher privilege levels. A TEE as an isolated execution environment provides security features such as isolated execution, integrity of applications executing with the TEE, along with confidentiality of their assets. In general terms, the TEE offers an execution space that provides a higher level of security for trusted applications running on the device than a rich operating system (OS) and more functionality than a 'secure element' (SE).
InstantGo or InstantOn or Modern Standby is a Microsoft specification for Windows 8 hardware and software that aims to bring smartphone-type power management capabilities to the PC platform, as well as increasing physical security.
The Intel Management Engine (ME), also known as the Intel Manageability Engine, is an autonomous subsystem that has been incorporated in virtually all of Intel's processor chipsets since 2008. It is located in the Platform Controller Hub of modern Intel motherboards.
Custom firmware, also known as aftermarket firmware, is an unofficial new or modified version of firmware created by third parties on devices such as video game consoles and various embedded device types to provide new features or to unlock hidden functionality. In the video game console community, the term is often written as custom firmware or simply CFW, referring to an altered version of the original system software inside a video game console such as the PlayStation Portable, PlayStation 3, PlayStation Vita/PlayStation TV, PlayStation 4, Nintendo 3DS and Nintendo Switch. Installing custom firmware typically requires bootloader unlocking. The process of installing custom firmware is commonly referred to as "jailbreaking".

Librem is a line of computers manufactured by Purism, SPC featuring free (libre) software. The laptop line is designed to protect privacy and freedom by providing no non-free (proprietary) software in the operating system or kernel, avoiding the Intel Active Management Technology, and gradually freeing and securing firmware. Librem laptops feature hardware kill switches for the microphone, webcam, Bluetooth and Wi-Fi.

Bootloader unlocking is the process of disabling the bootloader security that makes secure boot possible. It can make advanced customizations possible, such as installing a custom firmware. On smartphones this can be a custom Android distribution or another mobile operating system. Some bootloaders are not locked at all, others can be unlocked using a standard command, others need assistance from the manufacturer. Some do not include an unlocking method and can only be unlocked through a software exploit.